Also, the discover tool is extremely valuable. We did evaluate Cylance and Carbon Black. Our environment has not changed drastically since our last review of it. We found that the latest modules needed additional tools to protect us. Not being able to complete the deployment in an efficient manner isone of the huge weaknesses. We wanted to come up with something that was a lot more adaptive toemerging world threats and notjust strictly signature-based. /FlateDecode >> That means all the security products, including the perimeter firewall, the DMZ. What are the pros and cons of Darktrace vs CrowdStrike Falcon vs alternative EPP solutions? How does Crowdstrike Falcon compare with FireEye Endpoint Security? It has allowed us to focus our efforts on other things relevant to how theoverall business functions. Learn how to automate your workflows, troubleshoot any issues, or get help from our support team. We had half of an FTE assigned to our antivirus prior to CrowdStrike. Early last year, they rolled out the ability to automate the sensor revision updates, but do it in a tiered fashion. If you took out the OverWatch feature then they should be about the same. For some reason, CrowdStrike does not provide any help in terms of how to deploy the agent in a more efficient manner. I would rate this solution as 10 out of 10. It was providing information about installed applications, account lockouts, and top console users. Our technology alliances, product integrations, and channel partnerships. Around 80% to 90% view of whatever it is happening with this endpoint, whatever action it is doing, can be inspected on the dashboard. Many companies acquire smaller companies to get a fraction of a piece of technology that tends to be an add-on or something that may compliment the core product, but CrowdStrike is making more strategic moves to acquire technology that they can directly integrate into the existing platform to make it even better and more effective. We scripted out a process in GPO, then we were able to deploy it fairly seamlessly. I do not care for a la carte pricing. You are looking at saving six to seven months of a person's time, collectively, which would have been spent on just doing this one function alone. That is just an added value. The NGAV portion is the most valuable feature. So, we have added that on, whichhas been valuable as well. Make the following changes to the config file: If you plan to use a proxy to connect to the Falcon Firehose endpoint, you will need to update http_proxy=. We aim to enable them to make that decision quicker by providing more information upfront. We also have team members that are capable ofconfiguring this product. Once the package was built to deploy to endpoints, we push the "Go" button.
They are usually very responsive. Provided there areno problems, when the next release happens, the N-1 versionwill automatically upstep my entire environment without having to put hands on it.
This product does notrequire any maintenance post-deployment. Also, there is a sales engineer who moderates the demonstration of the product. However, I realized in my previous organization when we had the full suite that there were a bunch of features in it that we didn't have time to operationalize. /etc/init.d/cs.falconhoseclientd start or service cs.falconhoseclientd start. Anything that is cloud-native, or has a cloud offering, will always get first billing over something that is on-prem. I have never had an issue with stability at my current organization. There is nothing existing today that I would change very much about the solution.
", "I would like them to improve the correlation of data in the search algorithms. In this regard, it has been relatively quiet. Once it is checked into the cloud, it updates, decides to download, and gets the new seamless version.
". So, that has been a big performance increase for us. The primary reason that we went with the product was their reputation. CrowdStrike seems to detect quite a bit more than McAfee did. equal to windows. So, better visibility of what doesn't have a sensor in our environment would be helpful. Having the cloud-based management console makes it a lot easier to maintain. I continue to see, especially in the last six months, that CrowdStrike is making very purposeful acquisitions to tactically and strategically build upon the platform. EDR was still kind of new then versus the traditional AV. The Prevent, EDR, and OverWatch are some of the biggest features for us. In total, we are protectingroughly 1500 endpoints. U.S. Venture has been using it since the first quarter of 2019. They have been able to offer Spotlight and other modules, which is great. This can be used to structure your incident data however youd like. These behaviors come through from CrowdStrike as a collection - so in Tines, we will break this down into individual events, so each one can be analyzed independently. You can do tens of thousands of hosts in less than a day. Getting the free trial was veryeasy. At the time, CrowdStrike was the leader. I would like to see a little bit more in the offline scanning ability. The reputation of the organization in the AV community. You installed it, then you connected to their cloud portal.
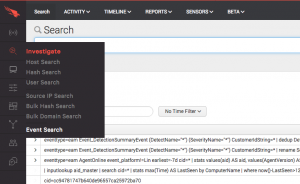
Well also drift into the world of response actions, which will allow analysts to contain the users device in CrowdStrike at the click of a button. Here you can see the configuration of that template. In my observation, there really isn't another company who can do as much as they can. Our main use case was looking for an endpoint solution that was able to follow our users anywhere. It does seem to pick up quite a bit, if not everything, that we have tested with it. One of the big value tickets: I don't have lists of hundreds of exceptions for certain applications that I have to maintain, add, delete, and move. This has done nothing but paid dividends since we have rolled it out. Each detection from CrowdStrike will create a new case in Jira. Standard FQL expression syntax follows the pattern:
:[operator] when filtering or selecting records. There are a lot of good and bad things that you can do with too strict or too loose of a policy governing workstations or servers. Within the course of just a few days, we were able to easily get CrowdStrike rolled out to about 300 machines. Here, we will extend this and build a Story that will connect to CrowdStrike, read new detections, and create a Jira ticket for each detection. KtTbH. They provide more granular details on the events that occurred on the host at the process level. It was just a matter of downloading a trial agent and setting it up. With our previous product, you had to be VPN'd and connected to our network. It's very time-consuming. 8i
AbxJ/= [~ V/I]
?ap^xC9I((]_4 We managed to deploy it to all our servers within a week or two. When Crowdstrike Falcon is set as an event source for InsightIDR, it only parses detection summary events by looking for DetectionSummaryEvent in the log line. No users have complained about any CPU spikes or false positives, which we like. Make sure you know what the policies do. At approximately 40% more, Falcon is probably too expensive compared to Cisco AMP and Cylance, although that is because of the OverWatch feature. I build a group, then I have to manually assign prevention policies, update policies, etc., but there is no function to copy that group. IT Security Analyst at U.S. Venture, Inc. 7 0 obj It took us less than an hour to deploy. We have that as part of our build process. I can cloud sandbox the endpoint, remediate it, and interact with it at the command line level remotely, regardless of where it is, as long as it has an Internet connection. So this makes sense for a smaller company like us. It takes a load off our hands as engineers and analysts. We are a heavy laptop environment. We spend about two hours a month for its care and feeding, which is really low maintenance. However, we have a tighter grip on updates for our server environment only because there was an issue at a point with one update. There is a lot of good technical detail, but in the position that I sit in, sometimes it is a little hard when I am not in it day in, day out to come to what is the real executive level sorts of things. The parsing technique used is the key value pair. Now, it has become a little bit of a crowded field and much more of a commodity but CrowdStrike was the industry leader when we were making our decision. We have looked at acquiring CrowdStrike's complete platform, which would be fully managed to deploy to that distributor network, which is about the same size as our corporate environment. I don't have to worry about any issues in our server rooms affecting the protection of the environment as a whole. I think that needs some help. Automatically creating cases in a centralized Case Management System will be the first step to reclaiming the time and energy of your Incident Responders. Therefore, we decided to change to itfrom Symantec. If it wasn't for them doing this, we would need at least a part-time FTE, if not a full-time, to operate and manage CrowdStrike keeping it up-to-date as well as the hygiene. Our administrators also loved that once they did this, they didnt have to deal with doing client upgrades once or twice a year, where you have to take servers down and reboot them. I want to see them continue to evolve, e.g., what other things can they disrupt which are operational things we have to continue to do as an organization.". So, it can get a little hectic. This just comes from my background in what I have done in other positions. It is fair, but I do not like how it is a la carte. Again, we will construct this using Jiras markdown syntax. To accomplish this, we defined the filter keyword as follows: Since we are performing a search where we want our attribute values to equal to our search string, we Three people were involved in deploying the solution: We have absolutely seen ROI, e.g.,the reduction in man-hours for resolving incidents. We haven't had cases where we have quarantined any material stuff yet, because we are relatively small and we don't see a lot of malware in our environment. The most common complaint from modern Incident Response teams is the volume of alerts that they receive. The solution is very scalable andeasy to deploy as well as sync up agents with it. The management was so cumbersome that there were only a handful of people able to resolve problems with endpoints or false detections. This Tines Story will pick up where the previous blog left off. What is the biggest difference between Carbon Black CB Defense, CrowdStrike, and SentinelOne? The very nature of the product has lessened my workload considerably. It helps to make sure you alwayshave an in-depth defensestrategy. ", "If we have a dashboard capability to uninstall agents, I think that would be great. Many of the worlds largest organizations already put their trust in CrowdStrike, including three of the 10 largest global companies by revenue, five of the 10 largest financial institutions, three of the top 10 health care providers, and three of the top 10 energy companies. In my previous organization had very much the same issue that my current one had. Pricing and licensing seem to be in line with what they offer.
The results from VirusTotal will contain some helpful information. << /Type /Page /Parent 2 0 R /Resources 4 0 R /Contents 3 0 R /MediaBox [0 0 595 842] You can begin your Tines journey from within the CrowdStrike Store. We should repeat this process for the parent process hash, too; it could help determine the severity of this issue. 
Sitemap 12