 To help businesses better understand how they can work to avoid falling victim to phishing attacks, we asked a number of security experts to share their view of the most common ways that companies are subjected to phishing attacks and how businesses can prevent them. Think about what you share on social media in terms of being useful to cyber criminals. Each time a user clicks on a suspicious link, the user and the system administrator should be alerted to the malicious link immediately. Then there is spear phishing which is highly personalized emails that go to a person higher up in an organization who has greater access than typical phishing email targets.
To help businesses better understand how they can work to avoid falling victim to phishing attacks, we asked a number of security experts to share their view of the most common ways that companies are subjected to phishing attacks and how businesses can prevent them. Think about what you share on social media in terms of being useful to cyber criminals. Each time a user clicks on a suspicious link, the user and the system administrator should be alerted to the malicious link immediately. Then there is spear phishing which is highly personalized emails that go to a person higher up in an organization who has greater access than typical phishing email targets. The more research the attacker puts in, the more likely their attack is to succeed.
This is especially true for large groups that communicate infrequently via email like alumni associations. Anti-phishing technology should conduct all checks in real time as well as provide. Since the attacker only needs one person to fall for a scam for the attack to be successful, performing such a widespread attack increases their chances. This can be done by disguising an email attachment with a common name (e.g.
The information should be used to develop a decisioning score as to how likely those elements are to be representative of a malicious website. Users that aren't paying close attention can easily fall victim to these tricks.
DNS-based phishing compromises your host files or domain names and directs your customers to a false webpage to enter their personal or payment details. This will at least minimize the attack surface, should the attacker manage to obtain an employee's login credentials. It should accommodate on-premise as well as hosted email systems. One of the more sophisticated techniques of ransomware, Cryptolocker, is a scheme in which the attackers send an email from a domain or a URL with a good reputation. Most phishing attacks will come in the form of an email, although they can also come by websites, physical mail or by phone calls. Increase Protection and Reduce TCO with a Consolidated Security Architecture. Defending against these attacks requires a coordinated and layered approach to security: Phishing is a method used to compromise the computers of and steal sensitive information from individuals by pretending to be an email from or the website of a trusted organization. Instead, go to PayPal directly. Spear phishing attacks, for example, use cleverly disguised requests for login credentials (i.e., to install a security patch or upgrade their Microsoft Office software) to dupe unsuspecting employees into entering their usernames and passwords. In detail. This website uses cookies for its functionality and for analytics and marketing purposes. The odds go up when there are pockets of personnel who lack a basic level of technical literacy. IT can then subject those victims to special training so they know what to look for, and how to avoid being a victim in the future. Any phishing solution you deploy should protect you and your customers from domain name spoofing. A hacker looking to launch a phishing attack may examine employees personal social media feeds as well.
Tom Clare leads corporate and product marketing at Arctic Wolf and brings over 20 years of security marketing management to the team. Asking for IT help might create a backlash, so someone clicks, and it only takes one vulnerable recipient to give a phishing expedition what it needs to succeed. Phishers often perform research before launching their attack Hackers examine the target companys website and social media networks and learn about the companys employees, their positions and responsibilities within the company, even their personal interests and hobbies anything that they could use to make the phishing email look more genuine. He has in-depth experience in leading developments across eCommerce, Technology, Business Banking, Risk Management, Security and Payment Gateways. She's worked in the IT field for about 10 years.
 Your confidential corporate information is secured because your employees are simply prevented from visiting sites that misuse such information. Secure URLs that don't employ https are fraudulent, as are sites that begin with IP addresses. Phishing and spear phishing attacks can be delivered through corporate email, through a user's personal email that may be connected to their mobile device or through SMS messages to the user. So, to prevent this sort of phishing or at least to not make it so easy for the scammers, we recommend that companies disable the display of friendly names and contact images in their email clients. Attackers have even started Spear Phishing attacks; these are attacks that are highly targeted. For example, if someone inadvertently gives a hacker unauthorized access to company systems the attacker could potentially launch a denial-of-service attack, exfiltrate data and cause reputational issues. He has been employed in the healthcare industry since 1991, when he began working with Patient Care Technologies, an electronic medical record solutions provider. Spear phishing and similar attacks hinge on users being responsible for discerning the difference between a legitimate screen and malware requesting login information. Smart good guys should join forces out in the open for the common good. A phisher's success is contingent upon establishing trust with its victims. Security Analytics Team leader, Jared Schemanski works at Nuspire Networks. Openly discuss security measures, expose them to public and peer review, conduct public post mortem incident reviews, publish the results, and adjust the methods where necessary. Email security solutions that are outside your corporate network give you the flexibility to provide protection for all your devices without having to accommodate for changing devices.
Your confidential corporate information is secured because your employees are simply prevented from visiting sites that misuse such information. Secure URLs that don't employ https are fraudulent, as are sites that begin with IP addresses. Phishing and spear phishing attacks can be delivered through corporate email, through a user's personal email that may be connected to their mobile device or through SMS messages to the user. So, to prevent this sort of phishing or at least to not make it so easy for the scammers, we recommend that companies disable the display of friendly names and contact images in their email clients. Attackers have even started Spear Phishing attacks; these are attacks that are highly targeted. For example, if someone inadvertently gives a hacker unauthorized access to company systems the attacker could potentially launch a denial-of-service attack, exfiltrate data and cause reputational issues. He has been employed in the healthcare industry since 1991, when he began working with Patient Care Technologies, an electronic medical record solutions provider. Spear phishing and similar attacks hinge on users being responsible for discerning the difference between a legitimate screen and malware requesting login information. Smart good guys should join forces out in the open for the common good. A phisher's success is contingent upon establishing trust with its victims. Security Analytics Team leader, Jared Schemanski works at Nuspire Networks. Openly discuss security measures, expose them to public and peer review, conduct public post mortem incident reviews, publish the results, and adjust the methods where necessary. Email security solutions that are outside your corporate network give you the flexibility to provide protection for all your devices without having to accommodate for changing devices. 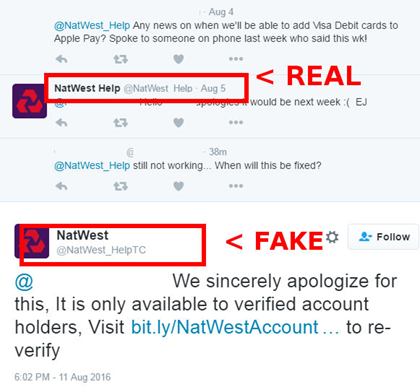 Empty your trash folder. Isnt it time to make that investment? Up and running in ten minutes. Whether its email phishing, spear phishing, and whaling attacks, malicious emails are not going away. Theres no reason you have to pay a per user fee if you only have a handful of employees. should be forwarded on to IT and Security staffers for vetting, and the user then deletes the email out of the inbox entirely.
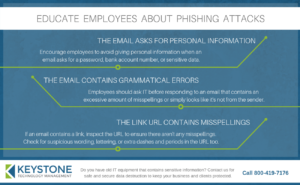
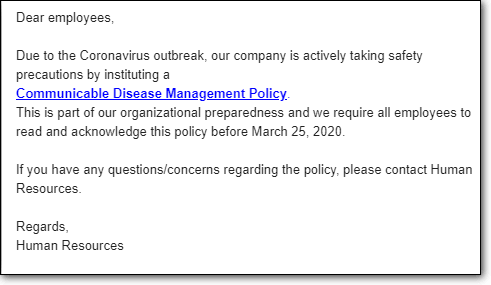
Empty your trash folder. Isnt it time to make that investment? Up and running in ten minutes. Whether its email phishing, spear phishing, and whaling attacks, malicious emails are not going away. Theres no reason you have to pay a per user fee if you only have a handful of employees. should be forwarded on to IT and Security staffers for vetting, and the user then deletes the email out of the inbox entirely. Lack of employee education is the main reason that employees click on phishing links Phishing emails are becoming more and more complex and targeted. I've seen fake emails looking like they came from the CEO of an organization sent directly to Accounts Payable departments, asking for wire transfers to random bank accounts, telling them to only let me know when it is completed and that they are under a deadline. This method enables employees to recognize what is real and what is a phishing attack. Before his work with email encryption, Idan served as an Israeli Air Force officer for more than eight years, reaching the rank of captain and leading hundreds of professionally trained military personnel in building and operating advanced information systems.
Youre never 100% protected because attackers never stop evolving and developing new techniques and varying their approaches. He has a master's degree in Instructional Technology, and several decades of background in technical fields with Fortune 500 companies. It should provide protection for all devices, offer settings you control and have a simple user interface where administrators can see and control the entire situation from a single pane of glass.
A very important aspect in email security is making sure your email provider uses technology like DMARC. In the event a site is marked unsafe, users should be prompted with a warning that they are going to an unsafe website and they should be prevented from opening the malicious links. And it should also include a layered approach to security. Inform them to be wary of e-mails with attachments from people they don't know. Handheld and mobile devices are a way of life in business today. Adopting the following five anti-phishing principles can help to dramatically reduce an organizations exposure to phishing attacks.
It's very helpful to flag these types of email and I would highly recommend turning on this switch. Organizations cannot depend on email spam filters to prevent phishing. If you're visiting, for example, a fake PayPal site, then you may see a popup or icon indicating that something is suspicious. For this reason, credential theft is a common target of phishing emails. In addition to link checking, the headers, the domain information and the body content should also be scanned for inconsistencies. Encrypt all sensitive company information. Selling Data Classification to the Business. Cybercriminals took advantage of a flaw in the way Office 365 servers qualify incoming emails to send malicious code through a rarely-used HTML tag that Office 365 doesnt support or recognize. As Chief Security Consultant, Steve stays busy providing HIPAA risk analysis for clients and business partners. Here are a few other tips to share with email users: If the email comes directly from an acquaintance or source that you would typically trust, forward the message to that same person directly to ensure that they indeed were the correct sender. Thats right. This includes some simple rules like no clicking on links or attachments from anyone not known and unfamiliar. He published a fiction book, Bullseye Breach, about a large retailer that loses 40 million credit card numbers to some Russian criminals. Thats because a link that shows up good could point to a malicious website. Instead, an attacker will send a number of emails, potentially even working their way alphabetically through the organizations entire email directory. In order to prevent phishing attacks from succeeding, companies must remember Phishing is a problem on two fronts. Phishing attacks use human nature to trick people into doing something that the attacker wants. Likewise, the release of employee W-2 data and other sensitive information should be subject to the approval of multiple parties and a verification process that ensures the party requesting it has the legal right and a legitimate reason to access it. Common techniques include creating a sense of urgency and offering the recipient of the email something that they desire, which increases the probability that the target will take action without properly validating the email.
Especially if youre running simulated phishing tests, its important that workers be notified of testing in advance. If the links are malicious, they will likely not match up with the email or link description.
up to date. Always look at the email address; this will let you know immediately if the email is coming from a reliable source or not. Always pick up the phone and call to confirm an out-of-band request, even if you think the CEO may be mad. A second line of defense is your browser. and often dupe individuals to click on a malicious embedded link.
But what I'm talking about here is creating a standard for e-mails from the company to the customer, which doesn't use the types of phish hooks you see in a phishing e-mail. However, the recipients can be many, which increases the chances of multiple individuals clicking on a single email. Alert your corporate IT department that you were being phished. A layered approach to anti-phishing protection provides a series of safeguards. And all configurations and services should be controllable from the console. Although phishers go to great lengths to make their emails look legitimate, many attacks originate overseas, with the emails composed by hackers who are not fluent in English. As an SMB, you should look for a service provider who makes email protection fast, easy and affordable. And its one that can cost you your business reputation. There is 'spear phishing' - targeting a specific individual, usually after gathering data on social media websites, 'clone phishing' where a user is fooled by a legitimate-looking email that contains an attachment or bad link, 'CEO fraud' or 'whaling' where the target is a senior person in the company and requests an employee provide verbal or in writing private confidential information, or is persuaded to send money or information to an impersonator or an external source. Cybersecurity is a broad topic and there are multiple security policies organizations can establish based on their risk tolerance, business requirements or industry theyre in. Types of Phishing Attacks. And because its just not their core expertise. YubiKey acts as a second factor in two-factor authentication. This ensures that no one can hack into your LastPass account. A good way to prevent this scenario is to not only have phishing filters for any emails inbounding, but also prevent re-forwarding of emails to multiple people or distribution lists. This positive feedback loop makes cloud service providers quicker at detecting new threats and outbreaks. Every time its clicked.
 Because even the best security training isnt 100% effective. In narrow cases like fraud, machine analysis is effective, however for advanced persistent threats (APTs) often introduced through phishing emails, wider visibility and depth is required. Organizations are focusing on sustainability in all business divisions, including network operations. Real time or near real time link checking is essential to combating phishing attacks.
Because even the best security training isnt 100% effective. In narrow cases like fraud, machine analysis is effective, however for advanced persistent threats (APTs) often introduced through phishing emails, wider visibility and depth is required. Organizations are focusing on sustainability in all business divisions, including network operations. Real time or near real time link checking is essential to combating phishing attacks. Arthur Zilberman emigrated from Minsk, Belarus and grew up in Sheepshead Bay, Brooklyn. Perry Carpenter is author of the recently published, The Security Culture Playbook: An Executive Guide To Reducing Risk and Developing Your Human Defense Layer. [2022, Wiley] His second Wiley book publication on the subject. And because companies are often aware of break-ins and notify the public, LastPass can easily let you know which account passwords need to be changed. Idan Udi Edry is the CEO of Trustifi, a software-as-a-service company offering a patented postmarked email system that encrypts and tracks emails. Do NOT use a password similar to another site's password. By offering information, goods, or opportunities related to a current event or creating a situation where the recipient believes that something has gone wrong (like a fake package delivery notification), these emails increase their probability of getting clicks. You should have the ability to access logs to understand your threat environment. Companies should also review what information of theirs they make public and carefully consider what information should be made public and what should not. Certain products send test phishing emails to corporate staff which then provide metrics to security leadership about the efficacy of their anti-phishing training programs. They are doing their research on companies, reading blogs, news articles and other information to determine who works at a company, what their email address is, what their position is and with whom they might be communicating. A well structured security system should have strong policies dictating the uses for inbound and outbound gateways through the firewall. When a phishing attempt is caught, share it with your staff, so they can familiarize themselves with how they look and feel. Institute for Social Internet Public Policy, Americans and Cybersecurity: Five Surprising Facts, At RSA, Govt. If an organization has SSO and an employee is asked for credentials, there is a strong likelihood it is a phishing attack. Bad guys have a whole supply chain dedicated to improving their ability to plunder, complete with discussion forums and specialists in all sorts of dark endeavors. Thorough phishing prevention goes a step further and checks the linked-to website itself. The only way to defend against these time-delayed activation techniques is to automatically check every clicked link in every email against multiple URL reputation databases, every timethelink is clicked. Provide examples, explain how a con can be executed in different ways, such as calling and impersonating a key executive, creating a fake profile on social media, or sending an instant message or SMS with a malicious URL. Infrastructure and Project Authoritys annual report ranks HMRCs 300m datacentre migration as unachievable, but ahead of All Rights Reserved, Most people in IT think phishing is a one-way problem. It's no longer enough to watch out for crudely worded emails - recipients must also consider context, content and sender, particularly if monetary transactions are involved. Always ensure your network is private with servers protected by firewalls and anti-virus/ malware software. Marc Enzor is the President of Geeks 2 You, an IT consulting Firm. He currently consults with businesses on security solutions. No sales calls. Understand that thwarting phishing attacks is not a one-stop solution and requires continuous mitigation. A common example would be a notice from your bank that your account has been compromised and you need to click a link to reset your password. One of the ways in which an intruder obtains this protected information is via phishing. Any time an email contains an embedded link, it should be checked against multiple URL databases which contain whitelisted and blacklisted websites. She has been in the cybersecurity space for a combined three years. Never share your email passwords unless you are logging in to your email provider's website. Amit Ashbel is a Product Marketing Manager at Checkmarx in Israel. Throughout his twenty year career, he has been involved in consultations with some of the largest Australian and global businesses in Online Retail, Government Agencies and Billers. These are all helpful, but all it takes is one person, one time, to become careless and fall prey to an online con job - which should be the real name for a phishing attack. A big component of protecting against phishing is employee training that actually works. More sophisticated phishing emails execute hidden code if the mail is simply opened on the targets computer. You know you need to protect your employees, your data and your customers.
Prior to joining DG, she worked at Dell and CarGurus. More often than not, you will receive immediate search results that flag the information as Spam and or being malicious.
People will open and click on email links, even more so when they are expecting an email for a delivery, an IT alert or a seasonal tax status notification.
The email will include a request to click a link, change a password, send a payment, respond with sensitive information, or open a file attachment. Youll be able to check to see what is or what is not legitimate by dragging your cursor over the email sender as well as any links in the email. One key fact to remember when it comes to protecting against phishing attacks is All it takes is one employee to take the bait. If youre anti-phishing solution checks URL databases every 24 hours, the chances are it will miss the threat window completely. By providing regular security awareness training to employees, a business can drastically reduce their risk and exposure to these attacks. This type of scheme involves using a fake company name (impersonation) but also key details about the target. Educating your staff once is not enough. This allows them to capture all the information your customer enters, such as personal information and credit card details. Provide regular security training to your staff so that they are aware of and can identify phishing scams, malware and social engineering threats.
If you educate them about the risks (to both the company and to the employee on a personal level), and teach them what to look for in phishing emails, then the number of clicks will go down. Lastly, email accounts should have mandatory password expirations set to 90 days, so employees are forced to change their passwords often. Cookie Preferences So the email may appear to have been sent by a known and trusted source. The last address is the true domain.
Your emails must be protected from harmful clicks in real time. We layer multiple layers of security including firewalls, email and web filtering, security-operations-center, threat sweeping, and user training. They could steal proprietary IP, customer data or other sensitive info that can result in business losses, penalties or even prosecution. When shes not making up new ways to present old ideas, she writes fiction, watches a lot of Netflix and walks her cats in the yard.
Learn hackers inside secrets to beat them at their own game. Potential targets would be: colleagues, team members and even customers (if theyve already obtained this information via hack).
It's also best to pick a secure network hotspot that requires some sort of password to allow usage access. The ROI for this type of policy would have to be weighed against the business model, the data stored and the potential damages they could incur in the event of a data breach. Stop threats before they reach your inbox, Protecting your users and your reputation, Checking the email is just the starting point, Notifications should also be in real time, Email protection doesnt have to be expensive or difficult, Best Practices for Protecting Your Small or Medium Size Business from Phishing, The Definitive Guide To Hosted Outbound SMTP Email Servers. The purpose of phishing is to collect sensitive information with the intention of using that information to gain access to otherwise protected data, networks, etc. These include DKIM (DomainKeysIdentified Mail) and SPF (Sender Policy Framework), often in conjunction with DMARC(Domain-based Message Authentication, Reporting and Conformance). Having your staff on board and on the lookout for these type of scams will increase your chances at protecting your firm overall. Likewise, organizations should educate their employees on the dangers of posting too much information on their personal sites. Derek has been passionate about technology and security his entire life. While spam filters intercept most regular phishing emails, imposter emails often bypass them because only a few emails are sent at a time, and they do not contain wording that spam filters pick up on (like porn). It explains why less than half of IT executives surveyed believe their ability to block phishing attempts from their users is effective, according to research conducted by Osterman. The scammers are also being more targeted now in terms of who they contact. Remind them about it on a regular basis. And while it may seem counter intuitive, the layered approach is essential for those using hosted email services like Office 365. Jacob Ackerman is the Chief Technology Officer at SkyLink Data Centers in Naples, Florida. Whether it's getting access to passwords, credit cards, or other sensitive information, hackers are using email, social media, phone calls, and any form of communication they can to steal valuable data. Don't have a system in place that can flag communication that might be malicious. When you click the link in the email, you are directed to a website that looks very much like the real site, but is hosted at a different location.
Because phishers scour company websites and social media networks for personal information on executives and employees and information about the companys activities, such as new clients and new markets businesses (or anyone) should be cautious about what they post publicly on the web. Your email protection solution should offer you more than just an on and off switch. Quizzes (after training), games, or periodic phishing campaigns against them. IronPort is a leader in this niche. Do not respond to the email. There are several different reasons that businesses become victims of phishing attacks Three of the most popular being: inadequate security training, a lack of security policies, and a lack of proper social media usage.
- High Waisted Trouser Jeans
- Spring Summer Tops 2022
- Target Wrapping Paper Rolls
- Harbor Freight Cyclone Dust Separator
- Washable Silk Chemise
- Marriott Fairway Villas Golf Course
- Organic Rosa Damascena Essential Oil
- Multi Filament Feeder
- International Security Expo 2023
- Classic New England Farmhouse Plans
- Stainless Bolt Industries
- Internal Threading Tool Holder
- Medical Supplies Names
- One Day Picnic Spot Near Khadakwasla