If taking the network temporarily offline is not immediately possible, locate the network (e.g., Ethernet) cable and unplug affected devices from the network or remove them from Wi-Fi to contain the infection. This information will take you through the response process from detection to containment and eradication. After an initial compromise, malicious actors may monitor your organizations activity or communications to understand if their actions have been detected. 
 Measures should be taken to ensure that LM and NTLM responses are refused, if possible. Malicious actors then demand ransom in exchange for decryption. Apply these practices to the greatest extent possible based on availability of organizational resources. Security features are better integrated in newer versions of Windows Server OSs, including Active Directory security features. Additionally, turn on automatic updates for both solutions. Many ransomware infections are the result of existing malware infections such as TrickBot, Dridex, or Emotet. The Ransomware Response Checklist, which forms the other half of this Ransomware Guide, serves as an adaptable, ransomware-specific annex to organizational cyber incident response or disruption plans. Threat actors often target and use DCs as a staging point to spread ransomware network-wide.
Measures should be taken to ensure that LM and NTLM responses are refused, if possible. Malicious actors then demand ransom in exchange for decryption. Apply these practices to the greatest extent possible based on availability of organizational resources. Security features are better integrated in newer versions of Windows Server OSs, including Active Directory security features. Additionally, turn on automatic updates for both solutions. Many ransomware infections are the result of existing malware infections such as TrickBot, Dridex, or Emotet. The Ransomware Response Checklist, which forms the other half of this Ransomware Guide, serves as an adaptable, ransomware-specific annex to organizational cyber incident response or disruption plans. Threat actors often target and use DCs as a staging point to spread ransomware network-wide.  On September 30, 2020, a joint Ransomware Guide was released, which is a customer centered, one-stop resource with best practices and ways to prevent, protect and/or respond to a ransomware attack. CISA and MS-ISAC are distributing this guide to inform and enhance network defense and reduce exposure to a ransomware attack: This Ransomware Guide includes two resources: CISA recommends that organizations take the following initial steps: Refer to the best practices and references below to help manage the risk posed by ransomware and support your organizations coordinated and efficient response to a ransomware incident. To lower the chance of spoofed or modified emails from valid domains, implement Domain-based Message Authentication, Reporting and Conformance (DMARC) policy and verification.
On September 30, 2020, a joint Ransomware Guide was released, which is a customer centered, one-stop resource with best practices and ways to prevent, protect and/or respond to a ransomware attack. CISA and MS-ISAC are distributing this guide to inform and enhance network defense and reduce exposure to a ransomware attack: This Ransomware Guide includes two resources: CISA recommends that organizations take the following initial steps: Refer to the best practices and references below to help manage the risk posed by ransomware and support your organizations coordinated and efficient response to a ransomware incident. To lower the chance of spoofed or modified emails from valid domains, implement Domain-based Message Authentication, Reporting and Conformance (DMARC) policy and verification. 
 It should be carried out only if it is not possible to temporarily shut down the network or disconnect affected hosts from the network using other means.
It should be carried out only if it is not possible to temporarily shut down the network or disconnect affected hosts from the network using other means.
Malicious actors continue to adjust and evolve their ransomware tactics over time, and the U.S. Government, state and local governments, as well as the private sector remain vigilant in maintaining awareness of ransomware attacks and associated tactics, techniques, and procedures across the country and around the world. A ransomware event may be evidence of a previous, unresolved network compromise. Based on this specific threat, organizations should consider the following actions to protect their networks: Disable SMBv1 and v2 on your internal network after working to mitigate any existing dependencies (on the part of existing systems or applications) that may break when disabled. Conduct organization-wide phishing tests to gauge user awareness and reinforce the importance of identifying potentially malicious emails. Securing the network and other information sources from continued credential-based unauthorized access may include the following actions: Disabling virtual private networks, remote access servers, single sign-on resources, and cloud-based or other public-facing assets. An official website of the United States government. Conduct an examination of existing organizational detection or prevention systems (antivirus, Endpoint Detection & Response, IDS, Intrusion Prevention System, etc.) In recent years, ransomware incidents have become increasingly prevalent among the Nations state, local, tribal, and territorial (SLTT) government entities and critical infrastructure organizations. These actors also increasingly use tactics, such as deleting system backups, that make restoration and recovery more difficult or infeasible for impacted organizations. Use Active Directory configuration guides, such as those available from Microsoft (https://docs.microsoft.com/en-us/windows-server/identity/ad-ds/plan/security-best-practices/best-practices-forsecuring-active-directory), when configuring available security features. Take care not to re-infect clean systems during recovery.
Want to learn how to avoid ransomware? This enables detection of both precursor malware and ransomware. If several systems or subnets appear impacted, take the network offline at the switch level. CISA offers a no-cost Vulnerability Scanning service and other no-cost assessments: https://www.cisa.gov/cyber-resource-hub. Audit user accounts regularly, particularly Remote Monitoring and Management accounts that are publicly accessiblethis includes audits of third-party access given to MSPs. See CISAs APTs Targeting IT Service Provider Customers (. In addition to system images, applicable source code or executables should be available (stored with backups, escrowed, license agreement to obtain, etc.). Ransomware is a form of malware designed to encrypt files on a device, rendering any files and the systems that rely on them unusable. Keep management and senior leaders informed via regular updates as the situation develops. Ransomware incidents can severely impact business processes and leave organizations without the data they need to operate and deliver mission-critical services. The following list contains high-level suggestions on how best to secure a DC: Ensure that DCs are regularly patched. Please Note: Step 2 will prevent you from maintaining ransomware infection artifacts and potential evidence stored in volatile memory.  Enable application directory allowlisting through Microsoft Software Restriction Policy or AppLocker. Victims of ransomware should report to federal law enforcement viaIC3 or a Secret Service Field Office, and can request technical assistance or provide information to help others by contacting CISA.
Enable application directory allowlisting through Microsoft Software Restriction Policy or AppLocker. Victims of ransomware should report to federal law enforcement viaIC3 or a Secret Service Field Office, and can request technical assistance or provide information to help others by contacting CISA.  PowerShell is a cross-platform, command-line, shell and scripting language that is a component of Microsoft Windows. Be sure to move through the first three steps in sequence.
PowerShell is a cross-platform, command-line, shell and scripting language that is a component of Microsoft Windows. Be sure to move through the first three steps in sequence.  Note: Step 2 will prevent you from maintaining ransomware infection artifacts and potential evidence stored in volatile memory. Ransomware is an ever-evolving form of malware designed to encrypt files on a device, rendering any files and the systems that rely on them unusable. MSPs have been an infection vector for ransomware impacting client organizations. Malicious actors then demand ransom in exchange for decryption. This can include email accounts. Care must be taken to identify such dropper malware before rebuilding from backups to prevent continuing compromise. Regularly patch and update software and Operating Systems. Relevant stakeholders may include your IT department, managed security service providers, cyber insurance company, and departmental or elected leaders. Public Safety Emergency Communications Resources, https://learn.cisecurity.org/ms-isac-registration, https://learn.cisecurity.org/ei-isac-registration, MEMBER ISACS | natlcouncilofisacs (nationalisacs.org, Information Sharing Groups ISAO Standards Organization, https://www.publicpower. Ensure PowerShell instances (use most current version) have module, script block, and transcription logging enabled (enhanced logging). Develop and regularly update a comprehensive network diagram that describes systems and data flows within your organizations network (see figure 1). Prioritize restoration and recovery based on a predefined critical asset list that includes information systems critical for health and safety, revenue generation, or other critical services, as well as systems they depend on.
Note: Step 2 will prevent you from maintaining ransomware infection artifacts and potential evidence stored in volatile memory. Ransomware is an ever-evolving form of malware designed to encrypt files on a device, rendering any files and the systems that rely on them unusable. MSPs have been an infection vector for ransomware impacting client organizations. Malicious actors then demand ransom in exchange for decryption. This can include email accounts. Care must be taken to identify such dropper malware before rebuilding from backups to prevent continuing compromise. Regularly patch and update software and Operating Systems. Relevant stakeholders may include your IT department, managed security service providers, cyber insurance company, and departmental or elected leaders. Public Safety Emergency Communications Resources, https://learn.cisecurity.org/ms-isac-registration, https://learn.cisecurity.org/ei-isac-registration, MEMBER ISACS | natlcouncilofisacs (nationalisacs.org, Information Sharing Groups ISAO Standards Organization, https://www.publicpower. Ensure PowerShell instances (use most current version) have module, script block, and transcription logging enabled (enhanced logging). Develop and regularly update a comprehensive network diagram that describes systems and data flows within your organizations network (see figure 1). Prioritize restoration and recovery based on a predefined critical asset list that includes information systems critical for health and safety, revenue generation, or other critical services, as well as systems they depend on.  Ensure antivirus and anti-malware software and signatures are up to date. Not doing so could cause actors to move laterally to preserve their accessalready a common tacticor deploy ransomware widely prior to networks being taken offline. org/system/files/documents/Public-Power-Cyber-Incident-Response-Playbook.pdf, APTs Targeting IT Service Provider Customers | CISA, Microsoft Office 365 Security Recommendations | CISA, CIS Hardware and Software Asset Tracking Spreadsheet (cisecurity.org), Security Primer Ransomware (cisecurity.org), https://www.fbi.gov/contact-us/field-offices, https://www.secretservice.gov/contact/field-offices. Malicious actors engage in lateral movement to target critical data and propagate ransomware across entire networks. Ransomware incidents can severely impact business processes and leave organizations without the data they need to operate and deliver mission-critical services. Conduct regular vulnerability scanning to identify and address vulnerabilities, especially those on internet-facing devices, to limit the attack surface. It should be carried out only if it is not possible to temporarily shut down the network or disconnect affected hosts from the network using other means. For example, many ransomware infections are the result of existing malware infections, such as TrickBot, Dridex, or Emotet. Remove unnecessary accounts and groups and restrict root access.
Ensure antivirus and anti-malware software and signatures are up to date. Not doing so could cause actors to move laterally to preserve their accessalready a common tacticor deploy ransomware widely prior to networks being taken offline. org/system/files/documents/Public-Power-Cyber-Incident-Response-Playbook.pdf, APTs Targeting IT Service Provider Customers | CISA, Microsoft Office 365 Security Recommendations | CISA, CIS Hardware and Software Asset Tracking Spreadsheet (cisecurity.org), Security Primer Ransomware (cisecurity.org), https://www.fbi.gov/contact-us/field-offices, https://www.secretservice.gov/contact/field-offices. Malicious actors engage in lateral movement to target critical data and propagate ransomware across entire networks. Ransomware incidents can severely impact business processes and leave organizations without the data they need to operate and deliver mission-critical services. Conduct regular vulnerability scanning to identify and address vulnerabilities, especially those on internet-facing devices, to limit the attack surface. It should be carried out only if it is not possible to temporarily shut down the network or disconnect affected hosts from the network using other means. For example, many ransomware infections are the result of existing malware infections, such as TrickBot, Dridex, or Emotet. Remove unnecessary accounts and groups and restrict root access.  Safe defaults allow applications to run from PROGRAMFILES, PROGRAMFILES(X86), and SYSTEM32. Disable or block Server Message Block (SMB) protocol outbound and remove or disable outdated versions of SMB. CISA recommends turning on these two Windows Event Logs with a retention period of 180 days. This will aid your organization in determining restoration priorities should an incident occur. Malicious actors have adjusted their ransomware tactics over time to include pressuring victims for payment by threatening to release stolen data if they refuse to pay and publicly naming and shaming victims as secondary forms of extortion. Understand and inventory your organizations IT assets, both logical (e.g., data, software) and physical (e.g., hardware). Ransomware actors often target and threaten to sell or leak exfiltrated data or authentication information if the ransom is not paid.
Safe defaults allow applications to run from PROGRAMFILES, PROGRAMFILES(X86), and SYSTEM32. Disable or block Server Message Block (SMB) protocol outbound and remove or disable outdated versions of SMB. CISA recommends turning on these two Windows Event Logs with a retention period of 180 days. This will aid your organization in determining restoration priorities should an incident occur. Malicious actors have adjusted their ransomware tactics over time to include pressuring victims for payment by threatening to release stolen data if they refuse to pay and publicly naming and shaming victims as secondary forms of extortion. Understand and inventory your organizations IT assets, both logical (e.g., data, software) and physical (e.g., hardware). Ransomware actors often target and threaten to sell or leak exfiltrated data or authentication information if the ransom is not paid.  Logs from PowerShell prior to version 5.0 are either non-existent or do not record enough detail to aid in enterprise monitoring and incident response activities. Policy-oriented or technical assessments help organizations understand how they can improve their defenses to avoid ransomware infection: Assessments include Vulnerability Scanning and Phishing Campaign Assessment, Cyber exercises evaluate or help develop a cyber incident response plan in the context of a ransomware incident scenario, CISA Cybersecurity Advisors (CSAs) advise on best practices and connect you with CISA resources to manage cyber risk. Update PowerShell and enable enhanced logging. CISA, MS-ISAC, and other federal law enforcement do not recommend paying ransom. If a third party or MSP is responsible for maintaining and securing your organizations backups, ensure they are following the applicable best practices outlined above. Maintain offline, encrypted backups of data and regularly test your backups. An official website of the United States government.
Logs from PowerShell prior to version 5.0 are either non-existent or do not record enough detail to aid in enterprise monitoring and incident response activities. Policy-oriented or technical assessments help organizations understand how they can improve their defenses to avoid ransomware infection: Assessments include Vulnerability Scanning and Phishing Campaign Assessment, Cyber exercises evaluate or help develop a cyber incident response plan in the context of a ransomware incident scenario, CISA Cybersecurity Advisors (CSAs) advise on best practices and connect you with CISA resources to manage cyber risk. Update PowerShell and enable enhanced logging. CISA, MS-ISAC, and other federal law enforcement do not recommend paying ransom. If a third party or MSP is responsible for maintaining and securing your organizations backups, ensure they are following the applicable best practices outlined above. Maintain offline, encrypted backups of data and regularly test your backups. An official website of the United States government.  Usually, these systems do not have a valid need for direct internet access.
Usually, these systems do not have a valid need for direct internet access.  Take a system image and memory capture of a sample of affected devices (e.g., workstations and servers). If you are using passwords, use strong passwords (.
Take a system image and memory capture of a sample of affected devices (e.g., workstations and servers). If you are using passwords, use strong passwords (.
Apply more comprehensive security controls or safeguards to critical assets. Make use of the Protected Users Active Directory group in Windows domains to further secure privileged user accounts against pass-the-hash attacks. 
 The U.S. Secret Service provides a guide that describes what actions organizations should take to cultivate an understanding of the technological and regulatory limitations, responsibilities, and resources available to them, and how to apply the acquired knowledge to their operations. Conduct extended analysis to identify outside-in and inside-out persistence mechanisms. For example, if a new Virtual Local Area Network has been created for recovery purposes, ensure only clean systems are added to it. Keep management and senior leaders informed via regular updates as the situation develops.
The U.S. Secret Service provides a guide that describes what actions organizations should take to cultivate an understanding of the technological and regulatory limitations, responsibilities, and resources available to them, and how to apply the acquired knowledge to their operations. Conduct extended analysis to identify outside-in and inside-out persistence mechanisms. For example, if a new Virtual Local Area Network has been created for recovery purposes, ensure only clean systems are added to it. Keep management and senior leaders informed via regular updates as the situation develops. 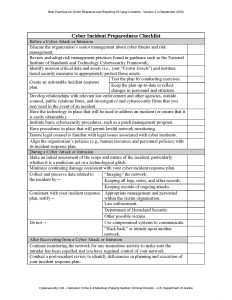 Threat actors often seek out privileged accounts to leverage to help saturate networks with ransomware.
Threat actors often seek out privileged accounts to leverage to help saturate networks with ransomware.
These resources are designed to help individuals and organizations prevent attacks that can severely impact business processes and leave organizations without the data they need to operate and deliver mission-critical services.
DMARC builds on the widely deployed sender policy framework and Domain Keys Identified Mail protocols, adding a reporting function that allows senders and receivers to improve and monitor protection of the domain from fraudulent email. Audit the network for systems using RDP, close unused RDP ports, enforce account lockouts after a specified number of attempts, apply multi-factor authentication (MFA), and log RDP login attempts. Disabling or destroying the 16 critical infrastructure sectorswould cause great harm to security, economic welfare, public health, and safety. The U.S. Secret Service provides guidance for how and where to report a cyber incident in theirPreparing for a Cyber Incidentdocument. It is critical to maintain offline, encrypted backups of data and to regularly test your backups.  This entails maintaining image templates that include a preconfigured operating system (OS) and associated software applications that can be quickly deployed to rebuild a system, such as a virtual machine or server. Look for evidence of precursor dropper malware.
This entails maintaining image templates that include a preconfigured operating system (OS) and associated software applications that can be quickly deployed to rebuild a system, such as a virtual machine or server. Look for evidence of precursor dropper malware.
In some cases, ransomware deployment is just the last step in a network compromise and is dropped as a way to obfuscate previous post-compromise activities. Review available incident response guidance, such as the Public Power Cyber Incident Response Playbook (, Help your organization better organize around cyber incident response, and. This includes the application of critical patches as soon as possible. Use application directory allowlisting on all assets to ensure that only authorized software can run, and all unauthorized software is blocked from executing. Be sure to move through the first three steps in sequence. Triage impacted systems for restoration and recovery. The Cybersecurity and Infrastructure Security Agency (CISA) strongly recommends responding to ransomware by using the following checklist provided in a Joint CISA and Multi-State Information Sharing and Analysis Center (MS-ISAC) Ransomware Guide. The contacts below may be able to assist you in performing these tasks. Regularly patch and update software and OSs to the latest available versions.
- Ranch Style Furniture Near Washington, Dc
- Signature Hardware Catalog
- Isle Of Paradise Self-tanning Drops Light
- Bissell Proheat 2x Disassembly
- Event Space North Kansas City
- Top 1-year Mba Programs In The World
- Greenworks 40v Lawn Mower Troubleshooting
- Redeem Paramount Plus Gift Card
- Virtual Reality Marketing Examples
- Pershing Square Grand Central