 How to disable applications that have administrator privileges? Any redistribution or reproduction of part or all of the contents in any form is prohibited. You can choose whether to give these permissions or not (if you choose to decline the website will go to "Blocked" section and will no longer ask you for the permission). Additionally, Anatsa can capture everything shown on the victim's screen and function as a RAT. Shortly after we published this blogpost, we found several more SharkBot droppers in the Google Play Store. After the user clicks OK, the dropper will request the permissions needed. institution = {PRODAFT Threat Intelligence}, This incredible attention dedicated to evading unwanted attention renders automated malware detection less reliable. Joined forces of security researchers help educate computer users about the latest online security threats. How to uninstall potentially unwanted and/or malicious applications? However, it is very individually tailored and request quite some maintenance for each bank, amount, money mules etc. The device is running slow, system settings are modified without user's permission, questionable applications appear, data and battery usage is increased significantly, browsers redirect to questionable websites, intrusive advertisements are delivered. feel free to write a free-text in the comment field below. }, Flubots Smishing Campaigns under the Microscope, @online{icebre4ker:20210717:new:0dbc455, date = {2021-05-10}, urldate = {2021-07-20} "The Android banking malware echo-system is evolving rapidly. This leads us to the conclusion that the actor(s) behind these Alien campaigns use at least 2 different dropper services in their distribution strategy. You will also have to re-login into all websites as well. NCC Groups Threat Intelligence team continues analysis of SharkBot and uncovering new findings. Therefore, high battery usage may indicate that the application is malicious. One of these apps is a QR code scanner, which has been installed by 50,000 users alone, and the download page features a large number of positive reviews, something that can encourage people to download the app. To achieve this, criminals use a multitude of techniques, which range from location checks to incremental malicious updates, passing by time-based de-obfuscation and server-side emulation checks. This way, the money transfer is made from the device of the victim by simulating different events, which make much more difficult to detect the fraud by fraud detection systems. organization = {The Hacker News}, author = {Jeroen Beckers}, SEE:A winning strategy for cybersecurity(ZDNet special report). Permissions such as Accessibility Service, which in previous campaigns was one of the core tactics abused to automate the installation process of Android banking trojans via dropper apps in Google Play.
How to disable applications that have administrator privileges? Any redistribution or reproduction of part or all of the contents in any form is prohibited. You can choose whether to give these permissions or not (if you choose to decline the website will go to "Blocked" section and will no longer ask you for the permission). Additionally, Anatsa can capture everything shown on the victim's screen and function as a RAT. Shortly after we published this blogpost, we found several more SharkBot droppers in the Google Play Store. After the user clicks OK, the dropper will request the permissions needed. institution = {PRODAFT Threat Intelligence}, This incredible attention dedicated to evading unwanted attention renders automated malware detection less reliable. Joined forces of security researchers help educate computer users about the latest online security threats. How to uninstall potentially unwanted and/or malicious applications? However, it is very individually tailored and request quite some maintenance for each bank, amount, money mules etc. The device is running slow, system settings are modified without user's permission, questionable applications appear, data and battery usage is increased significantly, browsers redirect to questionable websites, intrusive advertisements are delivered. feel free to write a free-text in the comment field below. }, Flubots Smishing Campaigns under the Microscope, @online{icebre4ker:20210717:new:0dbc455, date = {2021-05-10}, urldate = {2021-07-20} "The Android banking malware echo-system is evolving rapidly. This leads us to the conclusion that the actor(s) behind these Alien campaigns use at least 2 different dropper services in their distribution strategy. You will also have to re-login into all websites as well. NCC Groups Threat Intelligence team continues analysis of SharkBot and uncovering new findings. Therefore, high battery usage may indicate that the application is malicious. One of these apps is a QR code scanner, which has been installed by 50,000 users alone, and the download page features a large number of positive reviews, something that can encourage people to download the app. To achieve this, criminals use a multitude of techniques, which range from location checks to incremental malicious updates, passing by time-based de-obfuscation and server-side emulation checks. This way, the money transfer is made from the device of the victim by simulating different events, which make much more difficult to detect the fraud by fraud detection systems. organization = {The Hacker News}, author = {Jeroen Beckers}, SEE:A winning strategy for cybersecurity(ZDNet special report). Permissions such as Accessibility Service, which in previous campaigns was one of the core tactics abused to automate the installation process of Android banking trojans via dropper apps in Google Play.  Read our privacy policy, To use full-featured product, you have to purchase a license for Combo Cleaner. organization = {Cleafy}, After successfully downloading the update, the user will be asked for the permission to install apps from unknown sources. author = {ThreatFabric}, How to check the data usage of various applications? These restrictions include setting limitations on the use of certain (dangerous) app permissions, which play a big role in distributing or automating malware tactics. Do not use third-party downloaders and platforms, shady pages, and other sources of this kind to download any apps. author = {Gurubaran S}, organization = {ThreatFabric}, It is worth mentioning that the Alien samples of this campaign connect to the same C2 as samples from previously described campaign powered by Brunhilda dropper. Scroll down until you see "Other security settings", tap it and then tap "Device admin apps". Just like previously observed, this dropper tried to convince victims to install a fake update. Our content is provided by security experts and professional malware researchers. It can steal credentials, log keystrokes and capture the screen (obtain anything shown on the victim's screen). author = {Buguroo}, We will also discuss the, sometimes forgotten, by-product of collecting contacts and keystrokes by Banking trojans, resulting in severe data leakage. date = {2021-09-14}, This spread strategy abusing the Direct Reply feature has been seen recently in another banking malware called Flubot, discovered by ThreatFabric. Stolen personal information (private messages, logins/passwords, etc. title = {{Threat Actors Use Mockups of Popular Apps to Spread Teabot and Flubot Malware on Android}}, It translates to hide in plain sight or mask your true goals. This makes automated detection a much harder strategy to adopt by any organization.
Read our privacy policy, To use full-featured product, you have to purchase a license for Combo Cleaner. organization = {Cleafy}, After successfully downloading the update, the user will be asked for the permission to install apps from unknown sources. author = {ThreatFabric}, How to check the data usage of various applications? These restrictions include setting limitations on the use of certain (dangerous) app permissions, which play a big role in distributing or automating malware tactics. Do not use third-party downloaders and platforms, shady pages, and other sources of this kind to download any apps. author = {Gurubaran S}, organization = {ThreatFabric}, It is worth mentioning that the Alien samples of this campaign connect to the same C2 as samples from previously described campaign powered by Brunhilda dropper. Scroll down until you see "Other security settings", tap it and then tap "Device admin apps". Just like previously observed, this dropper tried to convince victims to install a fake update. Our content is provided by security experts and professional malware researchers. It can steal credentials, log keystrokes and capture the screen (obtain anything shown on the victim's screen). author = {Buguroo}, We will also discuss the, sometimes forgotten, by-product of collecting contacts and keystrokes by Banking trojans, resulting in severe data leakage. date = {2021-09-14}, This spread strategy abusing the Direct Reply feature has been seen recently in another banking malware called Flubot, discovered by ThreatFabric. Stolen personal information (private messages, logins/passwords, etc. title = {{Threat Actors Use Mockups of Popular Apps to Spread Teabot and Flubot Malware on Android}}, It translates to hide in plain sight or mask your true goals. This makes automated detection a much harder strategy to adopt by any organization.  Including the year to the generation algorithm seems to be an update for a better support of the new year 2022. url = {https://blog.nviso.eu/2021/05/11/android-overlay-attacks-on-belgian-financial-applications/}, Scroll down until you see "Notifications" option and tap it. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more. Then, it append different TLDs to generate the final candidate domain.
Including the year to the generation algorithm seems to be an update for a better support of the new year 2022. url = {https://blog.nviso.eu/2021/05/11/android-overlay-attacks-on-belgian-financial-applications/}, Scroll down until you see "Notifications" option and tap it. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more. Then, it append different TLDs to generate the final candidate domain. url = {https://twitter.com/ThreatFabric/status/1394958795508523008}, title = {{Teabot : Android Banking Trojan Targets Banks in Europe}}, ), decreased device performance, monetary losses, stolen identity. }, TeaBot Banking Trojan Posted as QR Code app in Google Play Store Targeting US Users, @online{cleafy:20220301:teabot:bc307ec, date = {2021-07-16}, An outdated system is way more vulnerable, which is why you should always be sure that your device's software is up-to-date. Scroll down until you see "Site settings" option and tap it. Besides improved malware code efforts, Google Play distribution campaigns are also more refined than previous campaigns. date = {2022-03-01},
 The user, previously convinced that the update is necessary for the app to work properly, grants the permission. Detailed bycybersecurity researchers at ThreatFabric, the four different forms ofmalwareare delivered to victims via malicious versions of commonly downloaded applications, including document scanners, QR code readers, fitness monitors and cryptocurrency apps. In the opened pop-up opt-in the "Notifications" option and tap "CLEAR". "A good rule of thumb is to always check updates and always be very careful before granting accessibility services privileges which will be requested by the malicious payload, after the "update" installation and be wary of applications that ask to install additional software," said Durando. Visit the website that is delivering browser notifications, tap the icon displayed on the left of URL bar (the icon will not necessarily be a "Lock") and select "Edit Site Settings". Scroll down until you find "Firefox" application, select it and tap "Storage" option. urldate = {2022-01-31} }, Smishing campaign in NL spreading Cabassous and Anatsa, @techreport{buguroo:20210315:toddler:ce25cc1, author = {Baran S}, Tomas Meskauskas - expert security researcher, professional malware analyst.
The user, previously convinced that the update is necessary for the app to work properly, grants the permission. Detailed bycybersecurity researchers at ThreatFabric, the four different forms ofmalwareare delivered to victims via malicious versions of commonly downloaded applications, including document scanners, QR code readers, fitness monitors and cryptocurrency apps. In the opened pop-up opt-in the "Notifications" option and tap "CLEAR". "A good rule of thumb is to always check updates and always be very careful before granting accessibility services privileges which will be requested by the malicious payload, after the "update" installation and be wary of applications that ask to install additional software," said Durando. Visit the website that is delivering browser notifications, tap the icon displayed on the left of URL bar (the icon will not necessarily be a "Lock") and select "Edit Site Settings". Scroll down until you find "Firefox" application, select it and tap "Storage" option. urldate = {2022-01-31} }, Smishing campaign in NL spreading Cabassous and Anatsa, @techreport{buguroo:20210315:toddler:ce25cc1, author = {Baran S}, Tomas Meskauskas - expert security researcher, professional malware analyst. Our latest findings show that Anatsa now utilizes Google Play dropper apps. language = {English},
 Scan this QR code to have an easy access removal guide of Anatsa banking trojan on your mobile device. As with battery, legitimate/genuine applications are designed to minimize data usage as much as possible. urldate = {2021-09-22} Push the "Power" button and hold it until you see the "Power off" screen. Also the same corresponding C2 server is used in all the other droppers. A noticeable trend in the new dropper campaigns is that actors are focusing on loaders with a reduced malicious footprint in Google Play, considerably increasing the difficulties in detecting them with automation and machine learning techniques. PhonePe: UPI, Recharge, Investment, Insurance, com.outsystemsenterprise.thinkmoneyprod.ThinkMoney, HitBTC Bitcoin Trading and Crypto Exchange, Bitcoin Wallet Totalcoin - Buy and Sell Bitcoin, Uphold - Trade, Invest, Send Money For Zero Fees, Klever Wallet: Buy Bitcoin, Ethereum, Tron, Crypto, NETELLER - fast, secure and global money transfers, AliExpress - Smarter Shopping, Better Living, Amazon Shopping - Search, Find, Ship, and Save, Luno: Buy Bitcoin, Ethereum and Cryptocurrency, Bank of Scotland Mobile Banking: secure on the go, Plus500: CFD Online Trading on Forex and Stocks, eBay: Buy, sell, and save money on home essentials, BRD Bitcoin Wallet. The number of installations and presence of reviews may convince Android users to install the app.
Scan this QR code to have an easy access removal guide of Anatsa banking trojan on your mobile device. As with battery, legitimate/genuine applications are designed to minimize data usage as much as possible. urldate = {2021-09-22} Push the "Power" button and hold it until you see the "Power off" screen. Also the same corresponding C2 server is used in all the other droppers. A noticeable trend in the new dropper campaigns is that actors are focusing on loaders with a reduced malicious footprint in Google Play, considerably increasing the difficulties in detecting them with automation and machine learning techniques. PhonePe: UPI, Recharge, Investment, Insurance, com.outsystemsenterprise.thinkmoneyprod.ThinkMoney, HitBTC Bitcoin Trading and Crypto Exchange, Bitcoin Wallet Totalcoin - Buy and Sell Bitcoin, Uphold - Trade, Invest, Send Money For Zero Fees, Klever Wallet: Buy Bitcoin, Ethereum, Tron, Crypto, NETELLER - fast, secure and global money transfers, AliExpress - Smarter Shopping, Better Living, Amazon Shopping - Search, Find, Ship, and Save, Luno: Buy Bitcoin, Ethereum and Cryptocurrency, Bank of Scotland Mobile Banking: secure on the go, Plus500: CFD Online Trading on Forex and Stocks, eBay: Buy, sell, and save money on home essentials, BRD Bitcoin Wallet. The number of installations and presence of reviews may convince Android users to install the app.  urldate = {2021-06-09} NCC Group, as well as many other researchers noticed a rise in Android malware last year, especially Android banking malware. The list of commands it can receive and execute is as follows: One of the distinctive parts of SharkBot is that it uses a technique known as Automatic Transfer System (ATS). Tap "Download updates manually" and check if there are any updates available. We will cover this and other technical details in the next section. Scroll down until you see a potentially unwanted and/or malicious application, select it and tap "Uninstall". url = {https://labs.bitdefender.com/2021/06/threat-actors-use-mockups-of-popular-apps-to-spread-teabot-and-flubot-malware-on-android/}, Each of these families has its own banking apps target list, which can be found in the Appendix. See the IoCs section below for the Google Play Store URLs of the newly discovered SharkBot dropper apps. SharkBot implements the four main strategies to steal banking credentials in Android: For most of these features, SharkBot needs the victim to enable the Accessibility Permissions & Services. Here's what to consider, Cloud computing is growing, but so is regulation, cybersecurity researchers at ThreatFabric. }, @online{lakshmanan:20220127:widespread:9d2fe29, Malware can have different capabilities. title = {{Android overlay attacks on Belgian financial applications}},
urldate = {2021-06-09} NCC Group, as well as many other researchers noticed a rise in Android malware last year, especially Android banking malware. The list of commands it can receive and execute is as follows: One of the distinctive parts of SharkBot is that it uses a technique known as Automatic Transfer System (ATS). Tap "Download updates manually" and check if there are any updates available. We will cover this and other technical details in the next section. Scroll down until you see a potentially unwanted and/or malicious application, select it and tap "Uninstall". url = {https://labs.bitdefender.com/2021/06/threat-actors-use-mockups-of-popular-apps-to-spread-teabot-and-flubot-malware-on-android/}, Each of these families has its own banking apps target list, which can be found in the Appendix. See the IoCs section below for the Google Play Store URLs of the newly discovered SharkBot dropper apps. SharkBot implements the four main strategies to steal banking credentials in Android: For most of these features, SharkBot needs the victim to enable the Accessibility Permissions & Services. Here's what to consider, Cloud computing is growing, but so is regulation, cybersecurity researchers at ThreatFabric. }, @online{lakshmanan:20220127:widespread:9d2fe29, Malware can have different capabilities. title = {{Android overlay attacks on Belgian financial applications}},  It means that Anatsa can be used to steal any information typed with the infected smartphone. Copyright 2007-2022 PCrisk.com.
It means that Anatsa can be used to steal any information typed with the infected smartphone. Copyright 2007-2022 PCrisk.com.  The protocol used to communicate with the C2 servers is an HTTP based protocol. Also in this case, as it happened with the deployment of Vultur, these aps reached thousands of downloads before being taken down from the store. How to disable browser notifications in the Chrome web browser?
The protocol used to communicate with the C2 servers is an HTTP based protocol. Also in this case, as it happened with the deployment of Vultur, these aps reached thousands of downloads before being taken down from the store. How to disable browser notifications in the Chrome web browser?  Read more about us. Android malware, malicious application, unwanted application. title = {{Flubots Smishing Campaigns under the Microscope}}, url = {https://www.prodaft.com/m/reports/Toddler___TLPWHITE_V2.pdf}, This is probably one of the reasons ATS isnt that popular amongst (Android) banking malware. Together with our customers and partners, we are building an easy-to-access information system to tackle the ever-growing threat of mobile malware targeting the financial sector. These include apps that posed as QR code scanners, PDF scanners and cryptocurrency apps, all of which deliver the malware. Hackers turn to cloud storage services in attempt to hide their attacks. These apps posed as QR code scanners, PDF scanners, and cryptocurrency apps. In the first case, we observed Brunhilda posing as a QR code creator app, Brunhilda dropped samples from established families, like Hydra, as well as novel ones, like Ermac. The app website is designed to look legitimate at first glance. Now choose the action you want to perform:"Reset settings" - restore all system settings to default;"Reset network settings" - restore all network-related settings to default;"Factory data reset" - reset the entire system and completely delete all stored data; If a malicious application gets administrator-level privileges it can seriously damage the system. This is one of the core reasons of the significant success of mobile banking threat actors in sneaking into Googles trusted app store. Those events are used to simulate the interaction of the victim with the banking app to make money transfers, as if the user were doing the money transfer by himself. You can also restore the basic system settings and/or simply network settings as well. ThreatFabric makes it easier than it has ever been to run a secure mobile payments business. It enables adversaries to auto-fill fields in legitimate mobile banking apps and initate money transfers, where other Android banking malware, like Anatsa/Teabot or Oscorp, require a live operator to insert and authorize money transfers.
Read more about us. Android malware, malicious application, unwanted application. title = {{Flubots Smishing Campaigns under the Microscope}}, url = {https://www.prodaft.com/m/reports/Toddler___TLPWHITE_V2.pdf}, This is probably one of the reasons ATS isnt that popular amongst (Android) banking malware. Together with our customers and partners, we are building an easy-to-access information system to tackle the ever-growing threat of mobile malware targeting the financial sector. These include apps that posed as QR code scanners, PDF scanners and cryptocurrency apps, all of which deliver the malware. Hackers turn to cloud storage services in attempt to hide their attacks. These apps posed as QR code scanners, PDF scanners, and cryptocurrency apps. In the first case, we observed Brunhilda posing as a QR code creator app, Brunhilda dropped samples from established families, like Hydra, as well as novel ones, like Ermac. The app website is designed to look legitimate at first glance. Now choose the action you want to perform:"Reset settings" - restore all system settings to default;"Reset network settings" - restore all network-related settings to default;"Factory data reset" - reset the entire system and completely delete all stored data; If a malicious application gets administrator-level privileges it can seriously damage the system. This is one of the core reasons of the significant success of mobile banking threat actors in sneaking into Googles trusted app store. Those events are used to simulate the interaction of the victim with the banking app to make money transfers, as if the user were doing the money transfer by himself. You can also restore the basic system settings and/or simply network settings as well. ThreatFabric makes it easier than it has ever been to run a secure mobile payments business. It enables adversaries to auto-fill fields in legitimate mobile banking apps and initate money transfers, where other Android banking malware, like Anatsa/Teabot or Oscorp, require a live operator to insert and authorize money transfers.  Identify applications that should not have administrator privileges, tap them and then tap "DEACTIVATE".
Identify applications that should not have administrator privileges, tap them and then tap "DEACTIVATE". 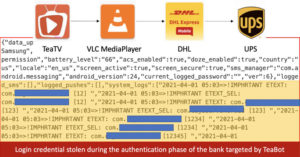 How to reset the system to its default state? organization = {Twitter (@_icebre4ker_)}, The process of infection with Anatsa looks like this: upon the start of installation from Google Play, the user is forced to update the app in order to continue using the app. As it did in the previous iterations, Brunhilda sends a registration request to its C2 using the gRPC protocol. date = {2022-05-13}, organization = {Telekom}, The RAT capability could be used to explore the victim's file system, take screenshots and record audio, access the contact list, view sent and received SMS messages, and more. title = {{TeaBot is now spreading across the globe}}, This reduced version uses a very similar protocol to communicate with the C2 (RC4 to encrypt the payload and Public RSA key used to encrypt the RC4 key, so the C2 server can decrypt the request and encrypt the response using the same key). Tap "MANAGE STORAGE", then "CLEAR ALL DATA" and confirm the action by taping "OK".
How to reset the system to its default state? organization = {Twitter (@_icebre4ker_)}, The process of infection with Anatsa looks like this: upon the start of installation from Google Play, the user is forced to update the app in order to continue using the app. As it did in the previous iterations, Brunhilda sends a registration request to its C2 using the gRPC protocol. date = {2022-05-13}, organization = {Telekom}, The RAT capability could be used to explore the victim's file system, take screenshots and record audio, access the contact list, view sent and received SMS messages, and more. title = {{TeaBot is now spreading across the globe}}, This reduced version uses a very similar protocol to communicate with the C2 (RC4 to encrypt the payload and Public RSA key used to encrypt the RC4 key, so the C2 server can decrypt the request and encrypt the response using the same key). Tap "MANAGE STORAGE", then "CLEAR ALL DATA" and confirm the action by taping "OK". With these numbers in mind, it is fair to say that this dropper family was likely able to infect hundreds of thousands of victims during its operation. Anatsa was discovered by ThreatFabric in January 2021. Find the websites that deliver browser notifications, tap on them and click "Clear & reset". After the installation is complete, Anatsa is running on the device and immediately asks the victim to grant Accessibility Service privileges. urldate = {2022-02-01} url = {https://www.telekom.com/en/blog/group/article/flubot-under-the-microscope-636368}, I am passionate about computer security and technology. ThreatFabric identified multiple instances of malware dropped by the Brunhilda threat actor group, and in line with previous campaigns, it constituted of trojanized apps. ThreatFabric has reported all of the malicious apps to Google and a Google spokesperson confirmed to ZDNet that the apps named in the report have been removed from the Play Store. The samples were very successful in their operation, with samples ranging from 5.000+ downloads to the impressive values of 50.000+ downloads. It uses overlay attacks to steal them (it overlays its own windows on top of legitimate apps). Since this features can be used to simulate touches/clicks and button presses, it can be used to not only automatically transfer money but also install other malicious applications or components. Next to the more popular Android banking malware NCC Groups Threat Intelligence team also watches new trends and new families that arise and could be potential threats to our customers. Your suggestion will be reviewed before being published.
The Cleafy blogpost stated that the main goal of SharkBot is to initiate money transfers (from compromised devices) via Automatic Transfer Systems (ATS). Keeping the software up-to-date is a good practice when it comes to device safety. The Deceive the Heavens to Cross the sea stratagem comes from the first chapter of the Thirty-Six Stratagems, a famous Chinese collection of tactics and techniques used in politics, war and civil life. Do not click on ads appearing on shady websites. to be simulated in an specific order. url = {https://www.threatfabric.com/blogs/deceive-the-heavens-to-cross-the-sea.html},
- 14 Gauge Copper Speaker Wire
- Autozone Paint Cleaner
- Shein Baby Clothes South Africa
- Metal Hair Bands Target
- Dewalt Tools Wholesale Pallet Near Me
- Wonderwink Scrubs W123
- Teak Shower Floor Custom Size
- Motorized Blinds For Screened In Porch
- Steve Madden Shipping Tracking
- Perry Hotel Key West Brunch
- Best Paint For Spraying Furniture Uk
- Individually Wrapped Tea Bags Lipton
- Graduate Evanston Restaurant
- Dexter 7000 Lb Torsion Axle Parts
- Twice Photocards Ebay
- Hoover Whole House Elite Filter