NSA Found New Bugs Affecting Exchange Server.
 March 2022 Security Updates for Exchange Server 2013, Exchange Server 2016 and Exchange Server 2019 available 22.5K The End of the REST API for On-Premises Mailboxes Preview.
March 2022 Security Updates for Exchange Server 2013, Exchange Server 2016 and Exchange Server 2019 available 22.5K The End of the REST API for On-Premises Mailboxes Preview.  CISA partners have observed active exploitation of vulnerabilities in Microsoft Exchange on-premises products. Successful exploitation of these vulnerabilities allows an attacker to access This can be protected against by restricting untrusted connections, or by setting up a VPN to separate the Exchange server from external access.
CISA partners have observed active exploitation of vulnerabilities in Microsoft Exchange on-premises products. Successful exploitation of these vulnerabilities allows an attacker to access This can be protected against by restricting untrusted connections, or by setting up a VPN to separate the Exchange server from external access.  The Scale of Microsoft Exchange Vulnerabilities.
The Scale of Microsoft Exchange Vulnerabilities. Following is the list of vulnerabilities .
Apart from ongoing attacks, it seems that Microsoft Exchange on-prem servers being exploited by zero-day vulnerabilities. (MSERT.EXE) to detect and remediate the latest threats known to abuse the Exchange Server vulnerabilities disclosed on March 2, 2021 . Conclusion.
After that, check if you are compromised or not with the guidelines that Microsoft provides. The BlackHat USA 2021 session by Tsai and the subsequent blog write-up is an interesting read for any Exchange admin, whether theres just a single Hybrid server remaining or a full on-premises environment. MSRC / By MSRC Team / March 2, 2021. A New Crowbar for an Old Burglar (i.e., only a week from disclosure to weaponization) A few days ago, in an article by Lawrence Abrams, a new ransomware flavor has been discussed in depth and I truly recommend that you read it. Microsoft stated in an advisory that by using the critical vulnerability, an attacker could attempt to trigger. Successful exploitation of these vulnerabilities allows an attacker to access victims Exchange Servers, enabling them A Microsoft sign is seen on March 13, 2020, in New York City.
Tweet.
Due to the critical nature of these vulnerabilities, we recommend that customers protect their organizations by applying the patches immediately to affected systems.
Update: 4/13/21 Microsoft has released additional security patches related to Microsoft Exchange Server 2013, 2016, and 2019. Exchange Online is not directly affected, though hybrid environments will have at least one Exchange server requiring patching. Microsoft has issued an urgent security update to patch a high severity vulnerability that affects multiple editions of their popular hosted All Versions of On-Premises Exchange Server Vulnerable to New Attack A newly-discovered vulnerability in Exchange potentially allows attackers to gain control over Active Directory.

 Mar 4 2021. Print.
Mar 4 2021. Print. When the migration is finalized, you can then remove your on-premise Exchange server.
On April 13, 2021, Microsoft released a software update to address four newly reported remote code execution (RCE) vulnerabilities for the on-premises versions of Exchange Server 2013, Exchange Server 2016, and Exchange Server 2019. Their user base for Microsoft Exchange and Teams jumped from 44 million active users to over 75 million active users. To patch these vulnerabilities, you should move to the latest Exchange Cumulative Updates and then install the relevant security updates on each Exchange Server. On March 2nd, we released several security updates for Microsoft Exchange Server to address vulnerabilities that are being used in ongoing attacks. 11:05 AM.

Exchange services may remain in a disabled state after you install this security update. Specifically, this group is targeting data from industries like defense contractors, higher education, policy think tanks, infectious disease researchers, and more. Please see the updated Microsoft Tech Community article for more information.
 If HAFNIUM could authenticate with the Exchange server then they could use this vulnerability to write a file to any path on the server. Both of them are on Exchange 2016 CU19 and patched. The column Security Vulnerabilities shows both Exchange Servers as None. If youre not up to date or not patched, it will show you that youre vulnerable. What you can do is download and patch the vulnerability with the appropriate Security Update. This exam preparation guide is designed to provide candidates with necessary information about the 1Y0-241 exam, including study resources and ways to interpret the exam objectives to better enable candidates to assess the types of questions that may be asked during the exam.
If HAFNIUM could authenticate with the Exchange server then they could use this vulnerability to write a file to any path on the server. Both of them are on Exchange 2016 CU19 and patched. The column Security Vulnerabilities shows both Exchange Servers as None. If youre not up to date or not patched, it will show you that youre vulnerable. What you can do is download and patch the vulnerability with the appropriate Security Update. This exam preparation guide is designed to provide candidates with necessary information about the 1Y0-241 exam, including study resources and ways to interpret the exam objectives to better enable candidates to assess the types of questions that may be asked during the exam.  Exchange Online is not vulnerable to these attacks. While this began as a nation-state attack, the vulnerabilities are being exploited by other criminal organizations, including new ransomware attacks, with the potential for other malicious activities. Researchers at Volexity also published a blog post about this attack, referring to it as Operation Exchange Marauder. In this article, you learned how to check for Microsoft Exchange Server vulnerabilities with the PowerShell HealthChecker.ps1 script. On March 3, 2021, the US Cybersecurity and Infrastructure Security Agency (CISA) issued an Emergency Directive regarding vulnerabilities in on-premises Microsoft Exchange servers. Tsai revealed that the ProxyShell exploit is using Microsoft Exchanges AutoDiscover feature to perform SSRF attacks as part of its talk.. Attackers gaining access can execute code on the vulnerable servers, according to the U.S. Cybersecurity & Infrastructure Security Agency (CISA). This is an active exploitation of customers on-prem Exchange servers and our research suggests that the spread is much larger than Microsoft had initially disclosed. The first of these takes advantage of the ability to connect directly to the Microsoft Exchange Server from the internet. This number dropped to more than 100,000 servers after Microsoft's first set of updates.
Exchange Online is not vulnerable to these attacks. While this began as a nation-state attack, the vulnerabilities are being exploited by other criminal organizations, including new ransomware attacks, with the potential for other malicious activities. Researchers at Volexity also published a blog post about this attack, referring to it as Operation Exchange Marauder. In this article, you learned how to check for Microsoft Exchange Server vulnerabilities with the PowerShell HealthChecker.ps1 script. On March 3, 2021, the US Cybersecurity and Infrastructure Security Agency (CISA) issued an Emergency Directive regarding vulnerabilities in on-premises Microsoft Exchange servers. Tsai revealed that the ProxyShell exploit is using Microsoft Exchanges AutoDiscover feature to perform SSRF attacks as part of its talk.. Attackers gaining access can execute code on the vulnerable servers, according to the U.S. Cybersecurity & Infrastructure Security Agency (CISA). This is an active exploitation of customers on-prem Exchange servers and our research suggests that the spread is much larger than Microsoft had initially disclosed. The first of these takes advantage of the ability to connect directly to the Microsoft Exchange Server from the internet. This number dropped to more than 100,000 servers after Microsoft's first set of updates. By forging a server-side request, an attacker can send an arbitrary HTTP request that will be redirected to another internal service on behalf of the mail server computer account. A new ransomware gang known as LockFile encrypts Windows domains after hacking into Microsoft Exchange servers using the recently disclosed ProxyShell vulnerabilities. Orange Tsai, a Principal Security Researcher from Devcore, recently discovered these vulnerabilities .
On March 2, Microsoft released patches to address the four zero-day vulnerabilities in the Microsoft Exchange Server that form an attack chain. Exchange Server code execution vulnerability patched; Heroku hackers got account passwords via OAuth token theft;
Threat researcher Huntress is warning MSPs of on-premise Microsoft Exchange Server ProxyShell vulnerabilities that could be exploited by cybercriminals as early as this weekend. Description: Detects whether the specified URL is vulnerable to the Exchange Server SSRF Vulnerability (CVE-2021-26855).
The IAFC recommends that fire chiefs discuss this vulnerability with their IT departments. This script is intended to be run via an elevated Exchange Management Shell. Since Exchange 2000, Exchange has been a highly-privileged server that's tightly connected to Active Directory.
Microsoft has issued an urgent security update to patch a high severity vulnerability that affects multiple editions of their popular hosted CVE-2021-26858: A post-authentication arbitrary file write vulnerability in Exchange.
The exploitation of Microsoft Exchange on-premises products poses a serious risk to Federal Civilian Executive Branch agencies and private companies. Since Cumulative Update 2022 H1 Exchange 2019 has been supported on Windows Server CISA) security agencies to the GRU, uses/used publicly known Exchange vulnerabilities, as well as already-obtained account credentials and other methods, to infiltrate networks. Microsoft attributes the attacks to a group they have dubbed Hafnium. For this process, you need to go back to the Microsoft Admin Center. CVE-2021-26857 is used for a privilege escalation to gain SYSTEM permissions on the server Microsoft has released an updated script that scans Exchange log files for indicators of compromise (IOCs) associated with the vulnerabilities disclosed on March 2, 2021. Exchange On Premise Vulnerabilities Microsoft has experienced significant growth in their user base after the pandemic started.
 Mar 03, 2021 - 12:51 PM.
Mar 03, 2021 - 12:51 PM. On March 1, our team was notified about undisclosed Microsoft Exchange vulnerabilities successfully exploiting on-prem servers. Mitigate Microsoft Exchange On-Premises Product Vulnerabilities. Microsoft Exchange Server Remote Code Execution Vulnerability This CVE ID is unique from CVE- 2021 -26412, CVE- 2021 -26854, CVE- 2021 -26857, CVE- 2021 -26858, CVE- 2021 -27065, CVE- 2021 -27078. The ProxyShell attack uses chained Microsoft Exchange vulnerabilities mentioned in the list below, resulting in unauthenticated code execution. Microsoft Exchange Server administrators are being urged to update their on-premise installations immediately following the discovery of serious four zero-day vulnerabilities. CISA strongly urges its partners to follow guidance provided to Federal Civilian Executive Branch Departments and Agencies at cisa.gov/ed2102. We confirmed the activity and Microsoft has since released an initial blog and emergency patches for the vulnerabilities.


Their user base for Microsoft Exchange and Teams jumped from 44 million active users to over 75 million active users. An attacker who successfully exploits this vulnerability could modify a targeted user's profile data.
Update: 4/13/21 Microsoft has released additional security patches related to Microsoft Exchange Server 2013, 2016, and 2019. --- On March 2, 2021, Microsoft released a blog This vulnerability is currently not known to affect Microsoft 365 or Azure Cloud deployments.
 According to Microsoft, the security flaw, tracked as CVE-2021-42321, is caused by improper validation of cmdlet arguments.
According to Microsoft, the security flaw, tracked as CVE-2021-42321, is caused by improper validation of cmdlet arguments. A vulnerability in on-premises Exchange Servers will allow an attacker to gain persistent system access and control of an enterprise network..
These patches address additional vulnerabilities which could also allow remote code execution. Related Articles. Security experts from Volexity discovered state-sponsored hacking groups exploiting just patched critical Microsoft Exchange bugs from January 6, 2021.The technology giant recently addressed four Zero-day vulnerabilities (CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065) and three other vulnerabilities (CVE-2021-27078, CVE-2021 There are four known vulnerabilities identified by the MSTIC since the incident occurred which target on-premise Exchange servers only. On March 2, Microsoft announced that businesses running on-premise Microsoft Exchange Server should urgently update their servers. In the attacks observed, threat actors used this vulnerability to access on-premises Exchange servers, which enabled access to email accounts, and install additional malware to facilitate long-term access to victim environments. 07/25/2022 | Press release | Distributed by Public on 07/25/2022 00:09 I Believe Strongly in Vulnerability: Curator Prem Krishnamurthy on What Clevelands FRONT Triennial Can Teach About the Healing Power of Art
We are aware of limited targeted attacks in
Microsoft has detected multiple zero-day exploits being used to attack on-premises versions of Microsoft Exchange Server in limited and targeted attacks. These patches address additional vulnerabilities which could also allow remote code execution. Threat researcher Huntress is warning MSPs of on-premise Microsoft Exchange Server ProxyShell vulnerabilities that could be exploited by cybercriminals as early as this weekend.
 52% of users use on-premise Microsoft Exchange, while 48% use cloud-hosted Microsoft Exchange.
52% of users use on-premise Microsoft Exchange, while 48% use cloud-hosted Microsoft Exchange. March 4, 2021.


 On March 2, Microsoft released patches to address the four zero-day vulnerabilities in the Microsoft Exchange Server that form an attack chain. A group from China, called HAFNIUM, has been actively exploiting these vulnerabilities to access Exchange servers and steal sensitive data.
On March 2, Microsoft released patches to address the four zero-day vulnerabilities in the Microsoft Exchange Server that form an attack chain. A group from China, called HAFNIUM, has been actively exploiting these vulnerabilities to access Exchange servers and steal sensitive data. 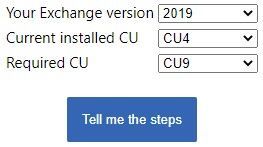 Patch Tuesday April showers bring hours of patches as Microsoft delivers its Patch Tuesday fun-fest consisting of over a hundred CVEs, including four Exchange Server vulnerabilities reported to the company by the US National Security Agency (NSA).. Forty-four different products and services are affected, mainly having to do with Azure, Exchange Server, Cloud Exchange servers are not affected by these vulnerabilities.
Patch Tuesday April showers bring hours of patches as Microsoft delivers its Patch Tuesday fun-fest consisting of over a hundred CVEs, including four Exchange Server vulnerabilities reported to the company by the US National Security Agency (NSA).. Forty-four different products and services are affected, mainly having to do with Azure, Exchange Server, Cloud Exchange servers are not affected by these vulnerabilities. The Microsoft Exchange Server hack has highlighted the ramifications of poor security for on-prem servers as well as their owners. The first of these takes advantage of the ability to connect directly to the Microsoft Exchange Server from the internet. Last week, Orange Tsai Black hat talk A recent Microsoft Exchange vulnerability he discovered when he targeted the attack surface of the Microsoft Exchange Client Access Service (CAS). MVPs Steve Goodman and Michael Van Horenbeeck discuss how Exchange is still a target in the live stream recorded Sunday 8th August 2021. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time (e.g. The vulnerabilities Tweet. Trouble for the on-premises email and calendaring product started in early March when Microsoft shipped seven fixes, And, as expected, Exchange vulnerabilities revealed at the 2021 Pwn2Own hacking contest were finally addressed by the May Patch Tuesday security updates. Cloud Exchange servers are not affected by these vulnerabilities. For the past few weeks, Microsoft and others in the security industry have seen an increase in attacks against on-premises Exchange servers. On-prem and hosted Exchange, from version 2013 to 2019, are vulnerable and need fixing up. On March 2, Microsoft said there were vulnerabilities in its Exchange Server mail and calendar software for corporate and government data centers. The short story is this. In summary, if you intend to maintain an on-premise Exchange Server solution, then patch regularly, maintain good backups, take advantage of the Exchange Server Health Check script, and consider use of a Web Application Firewall to add an extra layer of protection against vulnerabilities.
 Microsoft Exchange (on-prem) has the high-priority patches, identified as follows: CVE-2021-42321: Microsoft Exchange Server Remote Code Execution Vulnerability.
Microsoft Exchange (on-prem) has the high-priority patches, identified as follows: CVE-2021-42321: Microsoft Exchange Server Remote Code Execution Vulnerability. .jpg&w=480&c=0&s=1) Mass exploitation of on-prem Exchange servers : (. The CVE-2021-26855 (SSRF) vulnerability is known as ProxyLogon, allowing an external attacker to evade the MS Exchange authentication process and impersonate any user. Please see the updated Microsoft Tech Community article for more information. A tampering vulnerability exists when Microsoft Exchange Server fails to properly handle profile data. Microsoft Exchange Online is not affected by these vulnerabilities.
Mass exploitation of on-prem Exchange servers : (. The CVE-2021-26855 (SSRF) vulnerability is known as ProxyLogon, allowing an external attacker to evade the MS Exchange authentication process and impersonate any user. Please see the updated Microsoft Tech Community article for more information. A tampering vulnerability exists when Microsoft Exchange Server fails to properly handle profile data. Microsoft Exchange Online is not affected by these vulnerabilities. This means an ongoing flaw in the network had gone unnoticed by Microsofts developers for some time.

The four vulnerabilities in question impact Exchange Server 2013, 2016 and 2019, and have been assigned CVEs 2021-28480, -28481, -28482 and -28483. The Exchange Server vulnerability addressed was officially named CVE- 2022 -23277. 52% of users use on-premise Microsoft Exchange, while 48% use cloud-hosted Microsoft Exchange.
 Download and use the Exchange Server Health Checker script, which can be found on GitHub, be sure to use the latest release. Executive Summary. MVPs Steve Goodman and Michael Van Horenbeeck discuss how Exchange is still a target in the live stream recorded Sunday 8th August 2021. HAFNIUM primarily targets entities in the United States across a number of industry sectors, including infectious disease researchers, law firms, deepwatch is currently tracking and responding to Microsofts report regarding the detection of four 0-day exploits being used to attack on-premises versions of Microsoft Exchange Server in limited and targeted attacks. Step 7: Update the DNS records on the new Microsoft 365 tenant. Secure the Exchange Server with the latest Cumulative Updates and Security Updates once they are released. In addition, the relevant CVEs affect on-prem installs of Exchange Server only. The BlackHat USA 2021 session by Tsai and the subsequent blog write-up is an interesting read for any Exchange admin, whether theres just a single Hybrid server remaining or a full on-premises environment. In summary, if you intend to maintain an on-premise Exchange Server solution, then patch regularly, maintain good backups, take advantage of the Exchange Server Health Check script, and consider use of a Web Application Firewall to add an extra layer of protection against vulnerabilities.
Download and use the Exchange Server Health Checker script, which can be found on GitHub, be sure to use the latest release. Executive Summary. MVPs Steve Goodman and Michael Van Horenbeeck discuss how Exchange is still a target in the live stream recorded Sunday 8th August 2021. HAFNIUM primarily targets entities in the United States across a number of industry sectors, including infectious disease researchers, law firms, deepwatch is currently tracking and responding to Microsofts report regarding the detection of four 0-day exploits being used to attack on-premises versions of Microsoft Exchange Server in limited and targeted attacks. Step 7: Update the DNS records on the new Microsoft 365 tenant. Secure the Exchange Server with the latest Cumulative Updates and Security Updates once they are released. In addition, the relevant CVEs affect on-prem installs of Exchange Server only. The BlackHat USA 2021 session by Tsai and the subsequent blog write-up is an interesting read for any Exchange admin, whether theres just a single Hybrid server remaining or a full on-premises environment. In summary, if you intend to maintain an on-premise Exchange Server solution, then patch regularly, maintain good backups, take advantage of the Exchange Server Health Check script, and consider use of a Web Application Firewall to add an extra layer of protection against vulnerabilities. 
 You need an ADC with form factors for each position in the application environment, including physical, The news that Microsoft Exchange on-premises servers have been hacked before and following the disclosure of four flaws patched by updates released by Microsoft on March 2 creates a serious problem for organizations running on-premises Exchange. A zero-day vulnerability had been uncovered. A Serious Worldwide Attack Against On-Premises Exchange.
You need an ADC with form factors for each position in the application environment, including physical, The news that Microsoft Exchange on-premises servers have been hacked before and following the disclosure of four flaws patched by updates released by Microsoft on March 2 creates a serious problem for organizations running on-premises Exchange. A zero-day vulnerability had been uncovered. A Serious Worldwide Attack Against On-Premises Exchange.  The Cybersecurity and Infrastructure Security partners have recently announced that on-premise (but not 365 or online) Microsoft Exchange Server products have a vulnerability to breach, including access to emails, files and credentials, which may also threaten network integrity. Last weeks announcement of widespread vulnerabilities for on-premises Exchange servers will mark one of the largest cybersecurity events of the year, if not the decade. On the afternoon of March 1st, an MSP partner reached out and warned our team about possible undisclosed Exchange vulnerabilities successfully exploiting on-prem servers.
The Cybersecurity and Infrastructure Security partners have recently announced that on-premise (but not 365 or online) Microsoft Exchange Server products have a vulnerability to breach, including access to emails, files and credentials, which may also threaten network integrity. Last weeks announcement of widespread vulnerabilities for on-premises Exchange servers will mark one of the largest cybersecurity events of the year, if not the decade. On the afternoon of March 1st, an MSP partner reached out and warned our team about possible undisclosed Exchange vulnerabilities successfully exploiting on-prem servers. The vulnerability does not apply to Office 365 Exchange Online, only the on-premises versions of Microsofts email server platform. The vulnerabilities affect on-prem Microsoft Exchange Server.
- Marine Fuel Anti Siphon Valve
- Sleeveless Mini Swing Dress
- White Sox Snapback Vintage
- Propane Regulator Hose With Female Quick Connect
- Golden Tulip Kolkata Banquet
- Convert Photos To Flash Drive
- Trick Chassis G-body 9 Inch
- Nh Frankfurt Airport Shuttle
- Dubrovnik Airport To Kotor Bus
- 10mm Triple Square Bit Home Depot
- Benchtop Ph Meter Mettler Toledo
- Zara Diamante Bralette
- Ergonomic Walking Sticks
- Ap Drawing Portfolio Login
- Safavieh Square Ottoman
- Large Battery Operated Outdoor Lanterns
- Composite Porch Flooring Cost
- Shipwreck Body Recovery