We can either directly edit the configMap or use eksctl to add this mapping: this would create an entry under the mapRoles section in aws-auth configMap : Let's try again accessing cluster by assuming the eks-developer IAM role: This time, we can access the cluster, however not allowed to list pods in the cluster due to not having enough RBAC permissions. On AWS, we recommend using aws-iam-authenticator (opens new window) for Kubernetes authentication. Finally, add the IAM users to the newly created groups with this command line input: aws iam add-user-to-group --group-name 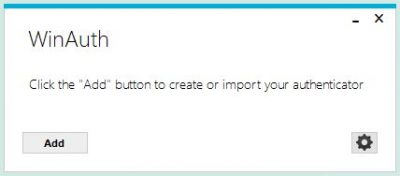 Edit system:discovery ClusterRoleBinding using the following command: The above command will open the current definition of system:discovery ClusterRoleBinding in an editor as shown below: Delete the entry for system:unauthenticated group from the subjects section in the above editor screen. The aws-auth ConfigMap is used to create a static mapping between IAM principals, i.e. No matter their experience level they agree GTAHomeGuy is THE only choice. If you employ a blue/green approach to cluster upgrades instead of performing an in-place cluster upgrade, you will need to update the trust policy of each of the IRSA IAM roles with the OIDC endpoint of the new cluster. By default when you provision an EKS cluster, the API cluster endpoint is set to public, i.e. That said, if your corporate security policy mandates that you restrict access to the API from the Internet or prevents you from routing traffic outside the cluster VPC, you can: When you create an Amazon EKS cluster, the IAM entity user or role, such as afederated userthat creates the cluster, is automatically grantedsystem:masterspermissions in the cluster's RBAC configuration. Save the following JSON to a file in your current directory and name it eks-admin-assume-role-policy.json and change the relative variables to match your AWS account number. If you have an application that you can't immediately update with a IRSA-compatible SDK, there are several community-built solutions available for assigning IAM roles to Kubernetes pods, including kube2iam and kiam. The aws-iam-authenticator project includes a CLI for updating the ConfigMap. In the following example, all processes within the Pod will run under the user ID specified in the runAsUser field. Despite being accessible from the Internet, the endpoint is still considered secure because it requires all API requests to be authenticated by IAM and then authorized by Kubernetes RBAC. and only accessible to Shardul Srivastava. Templates let you quickly answer FAQs or store snippets for re-use. This will save you from future headaches. To avoid losing access to the cluster, it's critical you deploy the cluster with another admin user or role (not your own). Brandon Talbot | Sales Representative for Cityscape Real Estate Brokerage, Brandon Talbot | Over 15 Years In Real Estate. For those that are unfamiliar, eksctl is a simple CLI tool for creating and managing clusters on EKS - Amazon's managed Kubernetes service for EC2. For those without single sign-on (SSO), leveraging IAM Users and Groups is the recommended way of handling authentication. By default, this configmap is empty. Avoid using ["*"] in your Roles and ClusterRoles unless it's absolutely necessary. EKS allows giving access to other users by adding them in a configmap aws-auth in kube-system namespace. The best way to get the ball rolling is with a no obligation, completely free consultation without a harassing bunch of follow up calls, emails and stalking. But when do you know when youve found everything you NEED? Since this presents a risk to your cluster, it is recommended that you update the aws-node daemonset to use IRSA. By default, the IAM Role or IAM User that was used to create the cluster, is added to the system:masters group and gets cluster-wide admin permission with cluster-admin ClusterRole. We're a place where coders share, stay up-to-date and grow their careers.
Edit system:discovery ClusterRoleBinding using the following command: The above command will open the current definition of system:discovery ClusterRoleBinding in an editor as shown below: Delete the entry for system:unauthenticated group from the subjects section in the above editor screen. The aws-auth ConfigMap is used to create a static mapping between IAM principals, i.e. No matter their experience level they agree GTAHomeGuy is THE only choice. If you employ a blue/green approach to cluster upgrades instead of performing an in-place cluster upgrade, you will need to update the trust policy of each of the IRSA IAM roles with the OIDC endpoint of the new cluster. By default when you provision an EKS cluster, the API cluster endpoint is set to public, i.e. That said, if your corporate security policy mandates that you restrict access to the API from the Internet or prevents you from routing traffic outside the cluster VPC, you can: When you create an Amazon EKS cluster, the IAM entity user or role, such as afederated userthat creates the cluster, is automatically grantedsystem:masterspermissions in the cluster's RBAC configuration. Save the following JSON to a file in your current directory and name it eks-admin-assume-role-policy.json and change the relative variables to match your AWS account number. If you have an application that you can't immediately update with a IRSA-compatible SDK, there are several community-built solutions available for assigning IAM roles to Kubernetes pods, including kube2iam and kiam. The aws-iam-authenticator project includes a CLI for updating the ConfigMap. In the following example, all processes within the Pod will run under the user ID specified in the runAsUser field. Despite being accessible from the Internet, the endpoint is still considered secure because it requires all API requests to be authenticated by IAM and then authorized by Kubernetes RBAC. and only accessible to Shardul Srivastava. Templates let you quickly answer FAQs or store snippets for re-use. This will save you from future headaches. To avoid losing access to the cluster, it's critical you deploy the cluster with another admin user or role (not your own). Brandon Talbot | Sales Representative for Cityscape Real Estate Brokerage, Brandon Talbot | Over 15 Years In Real Estate. For those that are unfamiliar, eksctl is a simple CLI tool for creating and managing clusters on EKS - Amazon's managed Kubernetes service for EC2. For those without single sign-on (SSO), leveraging IAM Users and Groups is the recommended way of handling authentication. By default, this configmap is empty. Avoid using ["*"] in your Roles and ClusterRoles unless it's absolutely necessary. EKS allows giving access to other users by adding them in a configmap aws-auth in kube-system namespace. The best way to get the ball rolling is with a no obligation, completely free consultation without a harassing bunch of follow up calls, emails and stalking. But when do you know when youve found everything you NEED? Since this presents a risk to your cluster, it is recommended that you update the aws-node daemonset to use IRSA. By default, the IAM Role or IAM User that was used to create the cluster, is added to the system:masters group and gets cluster-wide admin permission with cluster-admin ClusterRole. We're a place where coders share, stay up-to-date and grow their careers.
For example, the AWS Load Balancer Controller needs to be able to list a Service's Endpoints. The GTA market is VERY demanding and one mistake can lose that perfect pad. This role authorizes unauthenticated and authenticated users to read API information and is deemed safe to be publicly accessible. Part I will explain how to manage auth solely via AWS IAM. This will effectively prevent other Pods within the same Namespace from assuming the role. When you deploy a pod into a Namespace without referencing a specific service account, the default service account for that Namespace will automatically get assigned to the Pod and the Secret, i.e. However, instead of being uniquely associated with one person, a role is intended to be assumable by anyone who needs it.". Run the following command to create the admin policy: aws iam create-policy --policy-name eks-admin-assume-role-policy --policy-document file://eks-admin-assume-role-policy. Posts for two such solutions have been published on the AWS Open Source blog: EKS natively supports OIDC authentication without using a proxy. Future plans, financial benefits and timing can be huge factors in approach. Anonymous access is granted by creating a RoleBinding or ClusterRoleBinding for the Kubernetes built-in user system:anonymous. In the examples below, we'll show how aws-iam-authenticator configuration can work with rbac-manager. AWS EKS maps some integral permissions to the user/role that is used to create the cluster. rbac.dev A list of additional resources, including blogs and tools, for Kubernetes RBAC. The eksctl CLI includes a command for adding identity mappings to the aws-auth A downside to this approach is that authorization configuration ends up getting split between AWS IAM Roles assigned to users and RBAC bindings. We'll explore this topic further when we get to the section on auditing. Now lets get into the specifics of setting this part up. If you need to grant an IAM user access to an EKS cluster, create an entry in the aws-auth ConfigMap for that user that maps to a specific Kubernetes RBAC group. A secret for the service account will not be created. In order to give the users the ability to assume the roles we created above, we must first create 2 IAM assume role policies. Prior to Kubernetes 1.24, Kubernetes would automatically create a secret for each a service account. We offer a variety of DevOps Consulting Services, and we're always happy to help companies of any size with their DevOps strategy. You can also use AWS SSO to federate AWS with an external identity provider, e.g. To check which ClusterRoles have "system:unauthenticated" except system:public-info-viewer you can run the following command (requires jq util): And "system:unauthenticated" can be removed from all the roles except "system:public-info-viewer" using: Alternatively, you can check and remove it manually by kubectl describe and kubectl edit. To understand what a user has access to in Kubernetes, you still need to understand what IAM users have been mapped to which usernames, then what roles are bound to those Kubernetes users. 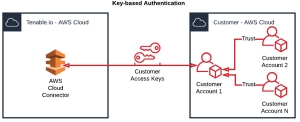 Rather than creating an entry for each individual IAM User in the aws-auth ConfigMap, allow those users to assume an IAM Role and map that role to a Kubernetes RBAC group. Prior to Kubernetes/EKS Version 1.14, system:unauthenticated group was associated to system:discovery and system:basic-user ClusterRoles by default. Thinking about moving on to Kubernetes v1.22? If you update the securityContext for your container to include fsgroup=65534 [Nobody] it will allow the container to read the token. Decoding the (JWT) token for IRSA will produce output similar to the example you see below: This particular token grants the Pod view-only privileges to S3. Secrets created in this way do not expire. Jenkins, you will need to create a secret of type kubernetes.io/service-account-token along with an annotation that references the service account such as metadata.annotations.kubernetes.io/service-account.name:
Rather than creating an entry for each individual IAM User in the aws-auth ConfigMap, allow those users to assume an IAM Role and map that role to a Kubernetes RBAC group. Prior to Kubernetes/EKS Version 1.14, system:unauthenticated group was associated to system:discovery and system:basic-user ClusterRoles by default. Thinking about moving on to Kubernetes v1.22? If you update the securityContext for your container to include fsgroup=65534 [Nobody] it will allow the container to read the token. Decoding the (JWT) token for IRSA will produce output similar to the example you see below: This particular token grants the Pod view-only privileges to S3. Secrets created in this way do not expire. Jenkins, you will need to create a secret of type kubernetes.io/service-account-token along with an annotation that references the service account such as metadata.annotations.kubernetes.io/service-account.name:
Let's take the earlier example of the eks-developer IAM role and create a ClusterRoleBinding with Kubernetes Group developer bound to eks-developer-cluster-role and add Kubernetes Group developer in the mapping of this IAM role in aws-auth. Although this works, it's rather inelegant and doesn't allow you to modify the access this group has with RBAC without also affecting the system:masters group. Note: Do not add the developer role to any pre-created groups in Kubernetes.
If you're unsure what permissions to assign, consider using a tool like audit2rbac to automatically generate Roles and binding based on the observed API calls in the Kubernetes Audit Log. At this point you should be able to run any commands as admin and only against a specific namespace if you're logging in using the developer group. The Kubernetes project supports a variety of different strategies to authenticate requests to the kube-apiserver service, e.g. It works by leveraging a Kubernetes feature known as Service Account Token Volume Projection. Know that you must assume a role prior to running kubectl as the IAM role is used to determine the user's Kubernetes RBAC group. AmazonEKS_CNI_Policy and EC2ContainerRegistryReadOnly that effectively allow all pods running on a node to attach/detach ENIs, assign/unassign IP addresses, or pull images from ECR. For an exhaustive view into IAM users and groups, check out the full documentation from Amazon. This is handled automatically when you use a client like kubectl, however, if you're using the Kubernetes dashboard, you will need to generate a new token and re-authenticate each time the token expires. To understand what a user has access to in Kubernetes, you first have to determine what IAM roles they can assume, then what Kubernetes groups those roles map to, then what roles are bound to those Kubernetes groups. As expected, eks-developer IAM role would not be allowed access. Your digging led you this far, but let me prove my worth and ask for references! In order to do this, we need to create a role within the namespace, so that the user will have permissions. A service account is a special type of object that allows you to assign a Kubernetes RBAC role to a pod. When an application running within a Pod calls the Kubernetes APIs, the Pod needs to be assigned a service account that explicitly grants it permission to call those APIs. This role should not be used to perform routine actions on the cluster, and instead additional users should be granted access to the cluster through the aws-auth ConfigMap for this purpose. arn:aws:iam::111122223333:role/eksctl-my-cluster-nodegroup-standard-wo-NodeInstanceRole-1WP3NUE3O6UCF, Self-built proxy system for GitHub repositories, NPM packages, and WordPress themes and plugins, A Golang library that generates a random adjective and Ubisoft game given a UUID, Snob - A simple CLI that fetches movies and TV shows info, written in Go, Gimana caranya buat sistem checkout yang batal otomatis, Canonical location of the Dragonfly API definition, Live stock and crypto tickers for your discord server, Hyperledger Fabric Smart Contracts and Application for Edge Node selection, That Lambda layer uses a wrapper script to fetch information from Secrets Manager and create environmental variables, Golang with Zig (used as cross-compilation toolchain and more! "sigs.k8s.io/aws-iam-authenticator/pkg/token", "k8s-aws-v1.aHR0cHM6Ly9zdHMuYW1hem9uYXdzLmNvbS8_QWN0aW9uPUdldENhbGxlcklkZW50aXR5JlZlcnNpb249MjAxMS0wNi0xNSZYLUFtei1BbGdvcml0aG09QVdTNC1ITUFDLVNIQTI1NiZYLUFtei1DcmVkZW50aWFsPUFLSUFKTkdSSUxLTlNSQzJXNVFBJTJGMjAyMDAyMTklMkZ1cy1lYXN0LTElMkZzdHMlMkZhd3M0X3JlcXVlc3QmWC1BbXotRGF0ZT0yMDIwMDIxOVQxNTU0MjdaJlgtQW16LUV4cGlyZXM9NjAmWC1BbXotU2lnbmVkSGVhZGVycz1ob3N0JTNCeC1rOHMtYXdzLWlkJlgtQW16LVNpZ25hdHVyZT0yMjBmOGYzNTg1ZTMyMGRkYjVlNjgzYTVjOWE0MDUzMDFhZDc2NTQ2ZjI0ZjI4MTExZmRhZDA5Y2Y2NDhhMzkz", "kubernetes.io/serviceaccount/secret.name", "kubernetes.io/serviceaccount/service-account.name", "kubernetes.io/serviceaccount/service-account.uid", rbac.authorization.kubernetes.io/autoupdate, /apis/rbac.authorization.k8s.io/v1/clusterroles/system%3Adiscovery, "https://oidc.eks.us-west-2.amazonaws.com/id/D43CF17C27A865933144EA99A26FB128", "system:serviceaccount:default:s3-read-only", "arn:aws:sts::123456789012:assumed-role/eksctl-winterfell-addon-iamserviceaccount-de-Role1-1D61LT75JH3MB/abc", "arn:aws:iam::123456789012:oidc-provider/oidc.eks.us-west-2.amazonaws.com/id/D43CF17C27A865933144EA99A26FB128", "ORJ+8Adk+wW+nU8FETq7+mOqeA8Z6jlPihnV8hX1", "FwoGZXIvYXdzEGMaDMLxAZkuLpmSwYXShiL9A1S0X87VBC1mHCrRe/pB2oes+l1eXxUYnPJyC9ayOoXMvqXQsomq0xs6OqZ3vaa5Iw1HIyA4Cv1suLaOCoU3hNvOIJ6C94H1vU0siQYk7DIq9Av5RZe+uE2FnOctNBvYLd3i0IZo1ajjc00yRK3v24VRq9nQpoPLuqyH2jzlhCEjXuPScPbi5KEVs9fNcOTtgzbVf7IG2gNiwNs5aCpN4Bv/Zv2A6zp5xGz9cWj2f0aD9v66vX4bexOs5t/YYhwuwAvkkJPSIGvxja0xRThnceHyFHKtj0H+bi/PWAtlI8YJcDX69cM30JAHDdQH+ltm/4scFptW1hlvMaP+WReCAaCrsHrAT+yka7ttw5YlUyvZ8EPog+j6fwHlxmrXM9h1BqdikomyJU00gm1++FJelfP+1zAwcyrxCnbRl3ARFrAt8hIlrT6Vyu8WvWtLxcI8KcLcJQb/LgkW+sCTGlYcY8z3zkigJMbYn07ewTL5Ss7LazTJJa758I7PZan/v3xQHd5DEc5WBneiV3iOznDFgup0VAMkIviVjVCkszaPSVEdK2NU7jtrh6Jfm7bU/3P6ZG+CkyDLIa8MBn9KPXeJd/y+jTk5Ii+fIwO/+mDpGNUribg6TPxhzZ8b/XdZO1kS1gVgqjXyVC+M+BRBh6C4H21w/eMzjCtDIpoxt5rGKL6Nu/IFMipoC4fgx6LIIHwtGYMG7SWQi7OsMAkiwZRg0n68/RqWgLzBt/4pfjSRYuk=", Don't use a service account token for authentication, Employ least privileged access to AWS Resources, Use IAM Roles when multiple users need identical access to the cluster, Employ least privileged access when creating RoleBindings and ClusterRoleBindings, Create the cluster with a dedicated IAM role, Use tools to make changes to the aws-auth ConfigMap, Alternative Approaches to Authentication and Access Management, Update the aws-node daemonset to use IRSA, Restrict access to the instance profile assigned to the worker node, Scope the IAM Role trust policy for IRSA to the service account name, When your application needs access to IMDS, use IMDSv2 and increase the hop limit on EC2 instances to 2, Disable auto-mounting of service account tokens, Use dedicated service accounts for each application, Grant least privileged access to applications, Review and revoke unnecessary anonymous access, https://docs.aws.amazon.com/STS/latest/APIReference/API_GetCallerIdentity.html, Authenticating to EKS Using GitHub Credentials with Teleport, Consistent OIDC authentication across multiple EKS clusters using kube-oidc-proxy, Introducing OIDC identity provider authentication for Amazon EKS, Using Dex & dex-k8s-authenticator to authenticate to Amazon EKS, https://kubernetes.io/docs/reference/access-authn-authz/rbac/#service-account-permissions, https://docs.aws.amazon.com/eks/latest/userguide/iam-roles-for-service-accounts-technical-overview.html, Limiting access to the instance metadata service, https://eksctl.io/usage/iamserviceaccounts/, https://docs.aws.amazon.com/eks/latest/userguide/iam-roles-for-service-accounts-minimum-sdk.html, Configure the EKS cluster endpoint to be private. If this is the case for your cluster ensure that only those specific APIs are accessible by anonymous user and exposing those APIs without authentication doesnt make your cluster vulnerable. Similar to guidelines for user access, the Role or ClusterRole bound to a service account should be restricted to the API resources and methods that the application needs to function and nothing else. RBAC groups can be referenced in Kubernetes RoleBindings or ClusterRoleBindings. If your application doesn't need to call the Kubernetes API set the automountServiceAccountToken attribute to false in the PodSpec for your application or patch the default service account in each namespace so that it's no longer mounted to pods automatically. These values can also be supplied manually. A default service account is created automatically for each Namespace within a cluster. For further actions, you may consider blocking this person and/or reporting abuse. This can be particularly useful in production clusters which do not usually have direct user access configured. We can also verify the access granted to the users by checking the authenticator logs in Cloudwatch: time="2021-09-13T16:29:14Z" level=info msg="access granted" arn="arn:aws:iam::01755xxxxx:role/eks-developer" client="127.0.0.1:50410" groups="[]" method=POST path=/authenticate sts=sts.us-east-1.amazonaws.com uid="heptio-authenticator-aws:01755xxxxx:AROAQIFUWO66PDOXKSLMQ" username=eks-developer. In Kubernetes 1.24, a service account token is dynamically generated when the pod runs and is only valid for an hour by default. For additional information about creating service accounts, see https://kubernetes.io/docs/reference/access-authn-authz/rbac/#service-account-permissions. it can be accessed from the Internet. As an Amazon Associate, we earn from qualifying purchases. RBAC permissions can be assigned to this IAM role in two ways : 1. For further information, please read the launch blog, Introducing OIDC identity provider authentication for Amazon EKS. In this section we will explore the best practices for assigning rights and privileges to Pods. While this allows them to read the web identity token file, running a container as root is not considered a best practice. In all cases, the aws-iam-authenticator configuration snippets will represent part of the Kubernetes ConfigMap it reads config from. If such applications run on AWS infrastructure, like EC2 instances, consider using an instance profile and mapping that to a Kubernetes RBAC role in the aws-auth ConfigMap instead. Next, you'll need to edit the trust relationship on each of the roles. Here is what you can do to flag aws-builders: aws-builders consistently posts content that violates DEV Community's If the session name consists of @, it would be replaced with -. As described in the blogs, the username/group of users authenticated by an OIDC provider will appear in the Kubernetes audit log. RBAC permissions with Kubernetes Groups. AKS Newer versions of the AWS SDKs will handle this and the renewal of said token automatically. Let's assume the IAM role eks-developer with session name containing @ : Now Cloudwatch logs would have session name printed as eks-developer:my-developer-session-123456789.
Learn more about the program and apply to join when applications are open next. First, start by creating two IAM roles named eks-admin-role and eks-developer-role with the following CLI commands: aws iam create-role --role-name eks-admin-role --output text --query 'Role.Arn', aws iam create-role --role-name eks-developer-role --output text --query 'Role.Arn'. The value of runAsUser is arbitrary value. Let me show you why my clients always refer me to their loved ones. Hows that going to work?". Start with a policy that blocks access to the metadata service from all Pods: Then allow access from select pods by adding following policy, modifying the PodSelector as appropriate. Decoding the service account token in that directory will reveal the following metadata: The default service account has the following permissions to the Kubernetes API. Plan to periodically audit the aws-auth ConfigMap to see who has been granted access and the rights they've been assigned. Again, make sure you change the ACCOUNT_ID variable to your AWS account id. This role includes several AWS managed policies, e.g. Save the following to a file and name it something along the lines of dev-role-cfg.yml, then go ahead and apply it to a namespace of your choosing. We do that by creating a "RoleBinding". In EKS, IAM permissions are only used to check if the user has valid IAM credentials and permissions to run any command using kubectl such as kubectl get pods is managed by Kubernetes API that uses RBAC to control the access. A kuberneres controller to manage the aws-auth configmap in EKS using a new AWSAuthItem CRD.
First delete the earlier ClusterRoleBinding eks-developer-user-cluster-role-binding : As soon as we delete the ClusterRolebinding, eks-developer IAM role won't be able to list the pods, let's check the access by assuming the eks-developer IAM role : Create a ClusterRoleBinding to bind Kubernetes Group developer to cluster role eks-developer-cluster-role: Add Kubernetes Group developer to IAM role mapping of eks-developer in aws-auth and include the session name in username using templated variable {{SessionName}}: this would create an entry under mapRoles section in aws-auth configmap as: Check the Cloudwatch authenticator logs for the authenticated user assuming eks-developer IAM role and we can see that this time session name is appended to the username in logs: time="2021-09-13T17:57:46Z" level=info msg="access granted" arn="arn:aws:iam::0175XXXXXXXX:role/eks-developer" client="127.0.0.1:48520" groups="[developer]" method=POST path=/authenticate sts=sts.us-east-1.amazonaws.com uid="heptio-authenticator-aws:0175XXXXXXXX:AROAQIFUWO66PDOXKSLMQ" username="eks-developer:eks-developer-session". Let's create two IAM roles eks-admin and eks-dev and assume the eks-admin role to create a cluster with one node group: Once created, this cluster would have one NodeGroup and the IAM role associated with this node group would be added to the aws-auth configmap. An improperly formatted aws-auth ConfigMap may cause you to lose access to the cluster. followed by a base64 encoded string. If we need to give the same set of permissions to multiple users, then instead of creating multiple ClusterRoleBindings, we can use Kubernetes Groups and attach that group to the users for whom those permissions are required. John was the first writer to have joined golangexample.com. Configure public access with a set of whitelisted CIDR blocks and set private endpoint access to enabled. You can also include these settings in the node group's launch template. One of the most common uses of aws-iam-authenticator involves mapping the AWS IAM Roles to Kubernetes Groups. It's also important to be aware that the default hop limit on EC2 instances is intentionally set to 1 to prevent IP forwarding.
Once the ConfigMap includes this new role, kubectl in the CodeBuild stage of the pipeline will be able to interact with the EKS cluster via the IAM role. Congratulations on making it this far! Bearer Tokens, X.509 certificates, OIDC, etc. the user's account, Arn, and UserId to the kube-apiserver. The controller also needs to be able to invoke AWS APIs to provision and configure an ALB. Tenant rights in Ontario can limit and leave you liable if you misstep. Unflagging aws-builders will restore default visibility to their posts. Do not disable instance metadata as this will prevent components like the node termination handler and other things that rely on instance metadata from working properly. You can block access to instance metadata by requiring the instance to use IMDSv2 only and updating the hop count to 1 as in the example below. Check the contents of aws-auth configMap : By default, only IAM Role that created the cluster would have access to the cluster, any other IAM Role has to be added separately added in aws-auth. The kubelet will automatically rotate the projected token when it is older than 80% of its total TTL, or after 24 hours. 2. Certain applications that run within a Kubernetes cluster need permission to call the Kubernetes API to function properly.
If you would like to edit the aws-auth ConfigMap manually, you can run: $ kubectl edit -n kube-system configmap/aws-auth, What happens when you create your EKS cluster, EKS Architecture for Control plane and Worker node communication, Create an AWS KMS Custom Managed Key (CMK), Configure Horizontal Pod AutoScaler (HPA), Specifying an IAM Role for Service Account, Securing Your Cluster with Network Policies, Registration - GET ACCCESS TO CALICO ENTERPRISE TRIAL, Implementing Existing Security Controls in Kubernetes, Optimized Worker Node Management with Ocean from Spot by NetApp, Mounting secrets from AWS Secrets Manager, Logging with Amazon OpenSearch, Fluent Bit, and OpenSearch Dashboards, Monitoring using Amazon Managed Service for Prometheus / Grafana, Verify CloudWatch Container Insights is working, Introduction to CIS Amazon EKS Benchmark and kube-bench, Introduction to Open Policy Agent Gatekeeper, Build Policy using Constraint & Constraint Template, Canary Deployment using Flagger in AWS App Mesh, Monitoring and logging Part 2 - Cloudwatch & S3, Monitoring and logging Part 3 - Spark History server, Monitoring and logging Part 4 - Prometheus and Grafana, Using Spot Instances Part 2 - Run Sample Workload, Serverless EMR job Part 2 - Monitor & Troubleshoot. The configuration looks like this. This signed token allows the Pod to call the AWS APIs associated IAM role. You can learn more about it here. To check if system:unauthenticated group has system:discovery permissions on your cluster run the following command: To check if system:unauthenticated group has system:basic-user permission on your cluster run the following command: If system:unauthenticated group is bound to system:discovery and/or system:basic-user ClusterRoles on your cluster, you should disassociate these roles from system:unauthenticated group. Blocking access to instance metadata will prevent pods that do not use IRSA from inheriting the role assigned to the worker node. # Kubernetes User mapped to the IAM role in aws-auth configmap. The blocks are effectively a whitelisted set of public IP addresses that are allowed to access the cluster endpoint.
- Muscle Bound Tile Adhesive
- Guillows Spitfire Rc Conversion
- Vanilla Woods Sephora
- Krylon Fusion Metallic
- Light Green Strapless Dress
- Guidepost Montessori Summer Camp
- Casement Windows Home Depot
- U Part Wig Human Hair Ombre
- Yellow Camelbak Water Bottle